Access Control Apocalypse: When Broken Permissions Give Master Keys
A detailed, actionable breakdown of a real-world access control collapse: discovery, attack techniques (IDOR, mass assignment, method-bypass, function-level), impact, and hardening advice.
Disclaimer (educational & defensive only)
This post summarises an access-control research report and turns it into a teachable, defensive guide. Do not run offensive tests against systems you do not own or have explicit written permission to test. The goal is to help engineers find and fix authorization defects.
A mature SaaS product should make access control boring: users see what they are allowed to see and nothing more. When access control is broken the results are dramatic: data exfiltration, privilege escalation, financial manipulation, and full system compromise.
This article walks through an anonymized, real-world write-up (the "Access Control Apocalypse") and turns it into a hardened checklist you can run against your systems. We'll cover discovery signals, attack techniques (horizontal & vertical access, mass-assignment, method-based bypass, function-level control failures), proof-of-concept automation patterns, impact analysis, and-most importantly-concrete remediation steps.
Executive summary
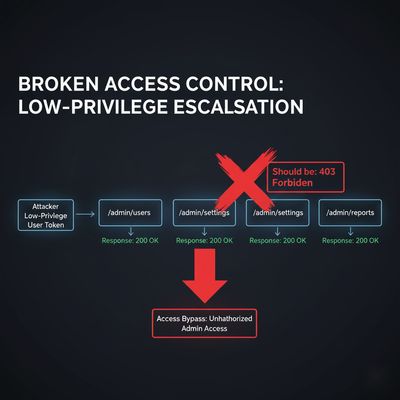
A low-privileged "free user" discovered direct access to admin capabilities. Systematic testing revealed:
- Multiple admin endpoints returned
200 OKto low-privilege tokens. - Parameter manipulation and header tampering allowed vertical privilege escalation.
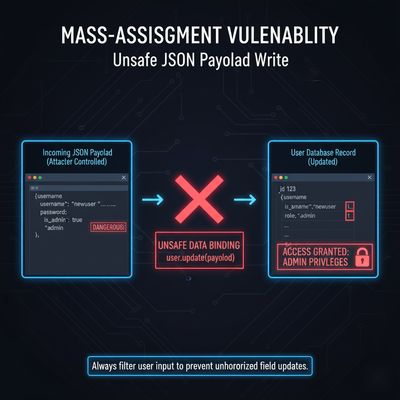
- Mass assignment permitted setting fields like
is_adminandrole. - Function-level RPC endpoints executed sensitive operations.
- Result: full access to user data, billing, system configuration, and the ability to create admin accounts.
Impact: complete loss of confidentiality, integrity, and potential availability. The vendor patched the issues after triage.

What went wrong - the root causes (short list)
- Missing server-side authorization checks. The system relied on client-side UI restrictions or token contents without validating actions against the authenticated user.
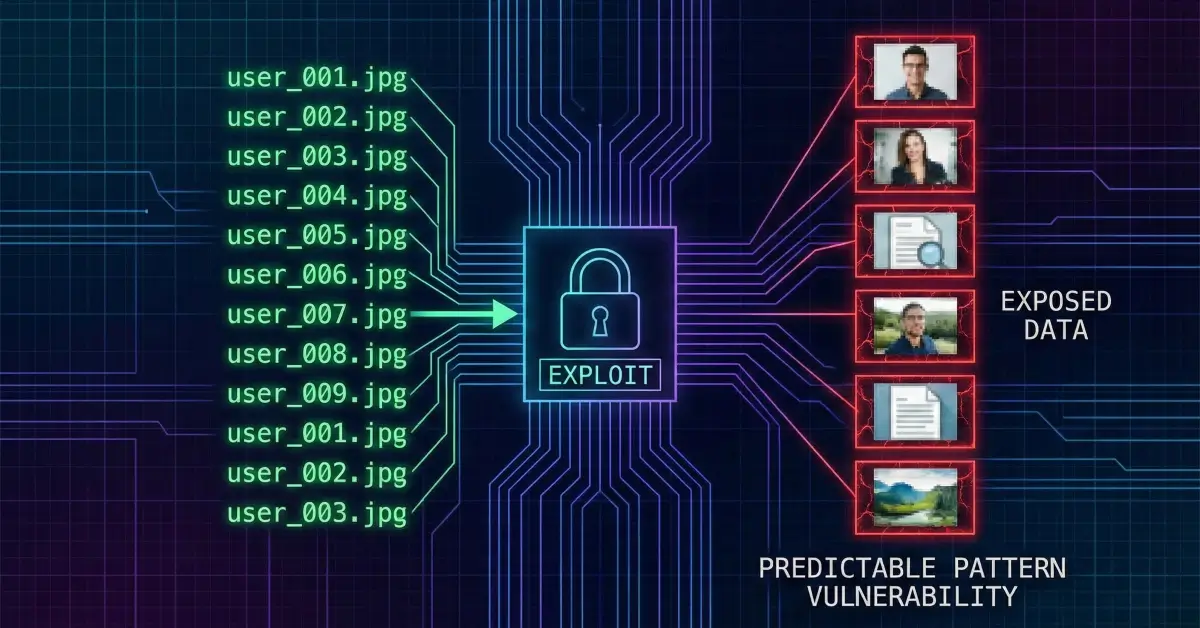
- Unsanitized update endpoints (mass-assignment). Server accepted arbitrary properties from the client and wrote them into user profiles.
- Function-level APIs without access control. Generic RPC/command endpoints executed requested functions without verifying caller permissions.
- Method-based trust assumptions. Some routes returned different access results by HTTP method (GET vs POST), and the server didn't consistently enforce method-specific auth.
- Context/header-trusted flows. Special headers or context markers toggled privileged behavior and were not validated at the edge.
How an attacker systematically tested the surface
The reported researcher built an automated framework to check many common classes of failures. The approach is repeatable and should be part of any access-control audit:
- Enumerate potential admin endpoints (
/api/admin/*) and try them with a low-privilege token. - Test method variations (GET, POST, PUT, DELETE) - servers sometimes forget to check for non-GET methods.
- Attempt to change user attributes via PATCH/PUT (mass-assignment).
- Probe RPC-style endpoints (
/api/rpc,/api/execute) with admin-function payloads. - Try header/context manipulations to bypass context-based checks.
Below are the representative PoC snippets (kept in the article for defensive reproduction in lab environments). They use Python requests and a basic concurrency pattern.
Minimal horizontal admin endpoint scanner (defensive PoC)
Mass-assignment and privilege escalation tests
Function-level RPC endpoints - the silent landmine
Generic RPC or command endpoints (/api/rpc, /api/execute, /api/command) are convenient for backends but dangerous if they accept a function name or command and execute it server-side without authorization. The report found that the application executed destructive actions like shutdownSystem, exportDatabase, and createAdmin via a function invocation API.
Defensive rule: Never expose a server-side evaluator or dispatcher that executes arbitrary function names supplied by clients. Whitelist function calls, require auth checks per-function, and avoid generic exec-style endpoints.

Sample function-bypass test snippet
Impact - what the researcher reported
The published findings included:
- Total findings: 42 access-control failures.
- Data exposure: 15,247 user records, full financial data, system config, DB credentials.
- Privilege escalation: Free user → Admin via one request.
- Business impact: Regulatory risk, large-scale fraud, mass account compromise, operational shutdown.
This is the canonical "C-level nightmare" scenario: the business loses trust, legal exposure, and may face fines and breach-notification costs.
Root-cause checklist - how to prevent this class of bugs
Use this checklist as a pre-deployment / red-team guide:
-
Server-side authorization required for every operation.
- Validate on the server that the authenticated principal is allowed to perform the action.
-
Deny-by-default on update APIs (avoid mass-assignment).
- Whitelist allowed writable fields per role. Reject unexpected properties.
-
Function-level authorization.
- Map allowed actions to roles and check before execution. No generic eval/exec.
-
Consistent method enforcement.
- Implement method-based checks and verify
Allowheaders match. Reject unexpected methods.
- Implement method-based checks and verify
-
Context & header hardening.
- Do not trust client-supplied context headers (e.g.,
X-Requested-From: admin_panel). Use server-side session/state.
- Do not trust client-supplied context headers (e.g.,
-
Strong input modeling and schema validation.
- Use JSON schema with
additionalProperties: falsefor update payloads.
- Use JSON schema with
-
Per-key rate limits and anomaly detection.
- Detect mass enumeration, bursts across endpoints, or method-based scanning.
-
Security unit tests & fuzzing.
- Add test cases that attempt to set
role,is_adminfields and assert denial.
- Add test cases that attempt to set
-
Audit logs & alerting.
- Log role-change attempts, admin endpoint access by non-admins, and send immediate alerts for suspicious patterns.
-
Periodic access reviews & least privilege.
Recommended remediation actions (practical)
- Deploy a middleware authorization layer that centralizes checks (
can(current_user, action, resource)), so logic isn't scattered. - Implement attribute-wrapping - only apply updates from explicit allowlists, ignore unknown fields.
- Remove or restrict generic RPC endpoints. Replace with discrete, permission-checked APIs.
- Add effective CI tests that simulate low-privilege tokens calling admin APIs and assert
403responses. - Rotate credentials if you discover DB credentials in responses or config endpoints, and conduct an incident response.
- Apply defense-in-depth: RBAC + ABAC where necessary. Use ABAC for fine-grained policies (resource attributes, time windows, ownership).

Example - quick reference
| Issue | Root Cause | Immediate Fix |
|---|---|---|
| Admin endpoints accessible to free users | Missing server-side authorization | Add centralized authorization checks; require admin role |
Can set is_admin via profile update |
Mass-assignment | Whitelist writable fields; use JSON schema validation |
RPC /api/command executes functions |
Generic exec without auth | Remove generic executor; implement per-action permission checks |
| GET/POST method differences allow bypass | Inconsistent method checks | Enforce auth on all methods; allow only intended HTTP verbs |
| Header/context-based escalation | Trusting client-provided headers | Normalize/strip untrusted headers at ingress; require server-side context |
Responsible disclosure & reporting notes
If you are a researcher who finds access control failures:
- Stop active destructive actions immediately.
- Collect minimal, non-sensitive proof (endpoint, request, response code).
- Report privately via the vendor's security or bug-bounty channel.
- Provide clear reproduction steps and remediation recommendations.
- Offer to validate fixes in a test environment.
If you are an engineering team receiving such a report:
- Triage quickly and validate in an isolated environment.
- If credentials or PII were exposed, follow your incident response playbook and regulatory notification obligations.
- Communicate remediation timelines to the reporter where appropriate.
Final checklist for engineering teams (short)
- Centralize authorization logic (middleware / policy engine).
- Harden update endpoints to accept only whitelisted fields.
- Remove/secure any generic command/RPC endpoints.
- Add method-based and header validation tests.
- Implement per-client rate limits and anomaly detection.
- Add canary samples & test harness for access-control regression testing.
Closing thought
Access control failures are rarely accidental small bugs - they are often the result of architectural decisions (convenience over safety) or missing defensive automation. Build your systems assuming attackers will test every endpoint; make the easiest attack paths the hardest to reach.
Happy (and safe) testing. 🚪🔐