
The $500 Stored XSS Bug in SideFX's Messaging System - Hacking the Inbox
A neutral, detailed write-up of a $500 stored XSS in SideFX messaging: technical PoC, impact analysis, defenses, and a reporter-ready template.
⚠️ Disclaimer
This article documents a vulnerability that was responsibly disclosed by a third-party researcher (handle: itriedallthenamess) and subsequently fixed by SideFX. The content below is educational and defensive. Do not attempt to exploit systems you do not own or have explicit permission to test. Follow each vendor’s responsible disclosure policies and applicable law.
Executive summary
A researcher found a Stored Cross-Site Scripting (XSS) issue in SideFX’s private messaging. SideFX stored user-supplied HTML in message bodies and rendered it to recipients without proper sanitization. The researcher demonstrated session-information exfiltration in a controlled proof-of-concept and received a $500 bounty. The underlying risk: once stored, a single payload can execute in many recipients’ browsers, enabling session theft, account takeover, or data exfiltration.
This article explains the vulnerability clearly, reproduces redacted PoCs (lab-safe), analyzes impact, and provides a prioritized remediation plan, detection suggestions, and a disclosure/report template for other hunters. It uses neutral, third-party reporting language (not first-person).
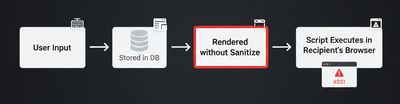
What is Stored XSS - a quick primer
Cross-Site Scripting occurs when an application sends back user input to browsers without proper encoding or sanitization, allowing malicious JavaScript to run. There are three common types:
- Reflected XSS: payload is included in a URL and executed when victims click it.
- DOM-based XSS: client-side scripts manipulate untrusted input into executable code.
- Stored XSS: the attacker’s input is persistently stored on the server (in messages, comments, profiles) and executes whenever another user views the stored content.
Stored XSS is particularly dangerous because a single stored payload may impact many users or high-privileged accounts (moderators, admins) who view the content.
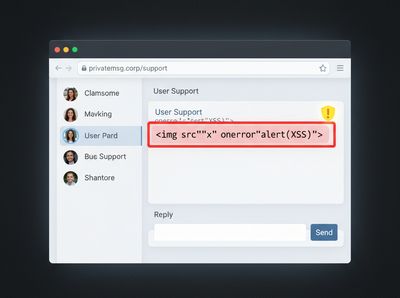
Summary of the SideFX issue
- Component: Private messaging system.
- Vulnerability: Stored XSS - message bodies accepted HTML and inline event attributes and rendered them without proper sanitization/escaping.
- Proof: researcher demonstrated
onerrorpayload execution and a controlled session-exfiltration PoC. - Impact: Session token access → possible full account takeover; mass exposure if administrators or many users viewed the message.
- Remediation: SideFX patched and awarded a $500 bounty.
How the researcher validated the flaw (redacted, safe PoC)
Safety note: Do NOT run these payloads against any real service unless you have permission. The following demonstrates the concept in an educational way and uses benign actions (alerts) for proof.
Minimal visible proof (non-destructive)
Send the following content in a message body to a test recipient:
When the recipient opens the message, the onerror handler triggers an alert() - a clear sign that script executed within the rendered message.
Conceptual exfiltration PoC (do not execute on live systems)
To demonstrate worst-case impact, the researcher showed how the attacker could read a same-origin resource (for example /account/sessions) and send it to a controlled endpoint. The sanitized conceptual form:
This works only if the victim’s browser can read /account/sessions (same origin and not blocked by CORS) and if the application doesn’t protect session tokens (e.g., HttpOnly flag). The example demonstrates the mechanism - exfiltrate sensitive data via an out-of-band channel.
Root cause analysis
The root causes observed:
- Unsafe rendering pipeline - message text was treated as HTML and injected into the page without escaping
</>and attribute boundaries. - Lack of HTML sanitization - the application didn’t remove dangerous tags or inline event handlers (e.g.,
onerror). - Insufficient policy controls - lack of CSP and lax protections allowed inline execution and easy exfiltration.
- Over-privileged client endpoints - an endpoint like
/account/sessionswas accessible to client code in a way that made exfiltration feasible in the PoC.
Fixing any one of these reduces the attack surface, but the recommended approach uses layered defenses.
Full impact breakdown
Stored XSS in messaging can lead to:
- Session theft / account takeover: If an attacker can read or coerce access to session tokens or authenticated endpoints, they can impersonate users.
- Mass compromise: Messages can be forwarded or visible to groups; a single stored payload can affect many users.
- Privilege escalation: If admins or moderators view messages via web UI, attackers can pivot to admin accounts.
- Data exfiltration: Private messages, files, and other sensitive data reachable via browser APIs can be extracted.
- Trust and legal risk: Exposure of private content leads to reputation damage and possible legal obligations.
Given these paths, OWASP classifies persistent XSS as a high-risk vulnerability in many contexts.

Reproduction checklist (responsible, for in-scope testing)
Only use this in authorized testing environments or labs.
- Create two accounts you control (sender & recipient).
- From sender account, send message body plain text containing the visible PoC. Example:
- Log in as recipient and open message. Capture a screenshot of the alert.
- Record request/response in Burp as evidence (redact tokens).
- Do not extract real user data for reporting; show non-destructive proof.
Practical advice for hunters - playbook
- Start in labs - PortSwigger, OWASP Juice Shop, DVWA. Learn safe patterns.
- Target likely sinks - messages, comments, profile bios, file upload names, signatures, and admin notes.
- Progressive payloads - test with
alert()first, then try attribute/DOM variants:onerror,<svg onload=>, broken attributes, and encoded forms. - Bypass techniques - entity encoding, attribute-breaking payloads, nested tags, and URL encoding can bypass naive filters. Use curated lists (PayloadsAllTheThings).
- Proof of impact - prefer non-destructive demos (alerts, console logs). If exfiltration is necessary for impact, use a controlled endpoint and coordinate with the vendor.
- Report clearly - steps to reproduce, sanitized PoC, impact summary, remediation suggestions.
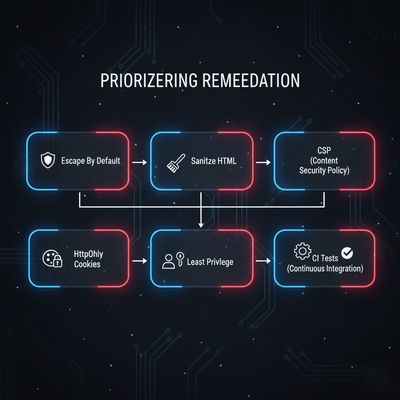
Engineering remediation - prioritized checklist
Implement these in order for best coverage:
- Escape by default - output user content as escaped text (HTML encode
& < > " ') unless HTML is required. - Sanitize HTML safely - if HTML is needed, use a reputable sanitizer (DOMPurify for JS, Bleach for Python, AntiSamy for Java) and whitelist allowed tags and attributes. Ensure event handlers (on*) are removed.
- Avoid dangerous features - prefer Markdown or restricted rich text; disallow raw HTML unless strictly necessary.
- Enforce CSP - add a strong Content Security Policy that blocks inline scripts (avoid
'unsafe-inline') and restricts script sources. - HttpOnly & Secure cookies - set
HttpOnlyandSecureon session cookies and applySameSitepolicies to reduce exfiltration via XSS. - Least privilege for endpoints - limit what data client-side code can access; avoid exposing session dumps to readable endpoints.
- Logging & monitoring - log suspicious inputs and alert on repeated script-like content in user fields.
- Automated tests - include XSS regression tests in CI (non-destructive test harnesses).
Detection & monitoring guidance
- Server-side detection: log payload patterns and flag repeated event-handler attributes (
onerror,onload,onclick). - WAF rules: add rules to detect common XSS patterns but do not rely solely on WAFs.
- Behavioral monitoring: alert on unusual downstream activity (requests to unknown third-party domains following message views).
- Client-side telemetry: instrument admin viewing pages to detect anomalies (e.g., sudden outbound requests).
Reporting template (copy-paste)
Use this template when filing reports:
Troubleshooting table (common issues when testing)
| Symptom | Cause | Recommended action |
|---|---|---|
| Alert does not appear | Message may be escaped or sanitized | Check page source (view-source) to see stored content; try encoded payloads |
| Payload removed on save | Server sanitization prevented it | Test alternative sinks or encoding techniques; avoid destructive tests |
| No exfiltration observed | Same-origin restrictions or HttpOnly cookie | Do not attempt further extraction; report impact based on feasible attack surface |
| WAF blocks attempts | Filtering at perimeter | Report detection details to vendor; adjust proof to non-destructive form |
Why $500? understanding bounty scales
Bounty sizes reflect program policy, expected attacker effort, and business risk. A $500 award for a stored XSS in a messaging system is consistent with a serious but scoped issue (privileged impact if admin accounts viewed messages). Larger programs or instances with greater user impact often pay more. Bounties are not the only measure of impact - real damage potential can vastly exceed monetary awards.

Final takeaways
- Stored XSS remains a high-risk web vulnerability because of its persistent and mass-impact nature.
- Messaging features are high-value targets; treat any user-supplied message content as highly untrusted.
- Proper sanitization, output encoding, and policy controls (CSP, HttpOnly cookies, least privilege) form a strong defense-in-depth posture.
- Hunters: practice in labs and always report responsibly.
Thanks to the researcher (handle: itriedallthenamess) for responsible disclosure, and to SideFX for timely remediation.
References & further reading
- PortSwigger Web Security Academy - XSS labs
- OWASP - XSS Prevention Cheat Sheet
- PayloadsAllTheThings - XSS payload collection
- DOMPurify, Bleach, AntiSamy - recommended sanitizers










