How to Test for IDOR: A Practical, Real-World Methodology for Security Testing
A beginner-to-advanced, real-world guide to finding Insecure Direct Object Reference (IDOR) vulnerabilities using a structured, ethical testing methodology.
Disclaimer
This article is strictly for educational and defensive purposes.
All techniques discussed must only be used on applications you own, have explicit permission to test, or that are in-scope for authorized bug bounty programs. Unauthorized testing is illegal.
Introduction
Insecure Direct Object Reference (IDOR) vulnerabilities are among the most common and most damaging issues found in modern web applications. Despite being well-known, they continue to appear in APIs, mobile backends, SaaS platforms, and internal tools.
Why?
Because IDOR is not a syntax bug.
It’s a logic failure.
Unlike injection flaws, IDOR doesn’t rely on clever payloads or bypassing filters. It exploits a simple assumption:
“If the user knows the object identifier, they must be allowed to access it.”
That assumption is wrong - and this guide will show you exactly how to test for it.
We’ll go step by step, from basic concepts to real-world workflows, in a way that mirrors how professional security testers and bug bounty hunters actually work.
What Exactly Is IDOR?
IDOR (Insecure Direct Object Reference) occurs when an application exposes a reference to an internal object and fails to verify whether the current user is authorized to access it.
Objects can include:
- User profiles
- Orders or invoices
- Files and documents
- Messages or chats
- Subscription settings
- Admin-only resources
If access control is missing or incorrectly implemented, changing that reference allows attackers to access or modify someone else’s data.
Why IDOR Is So Dangerous
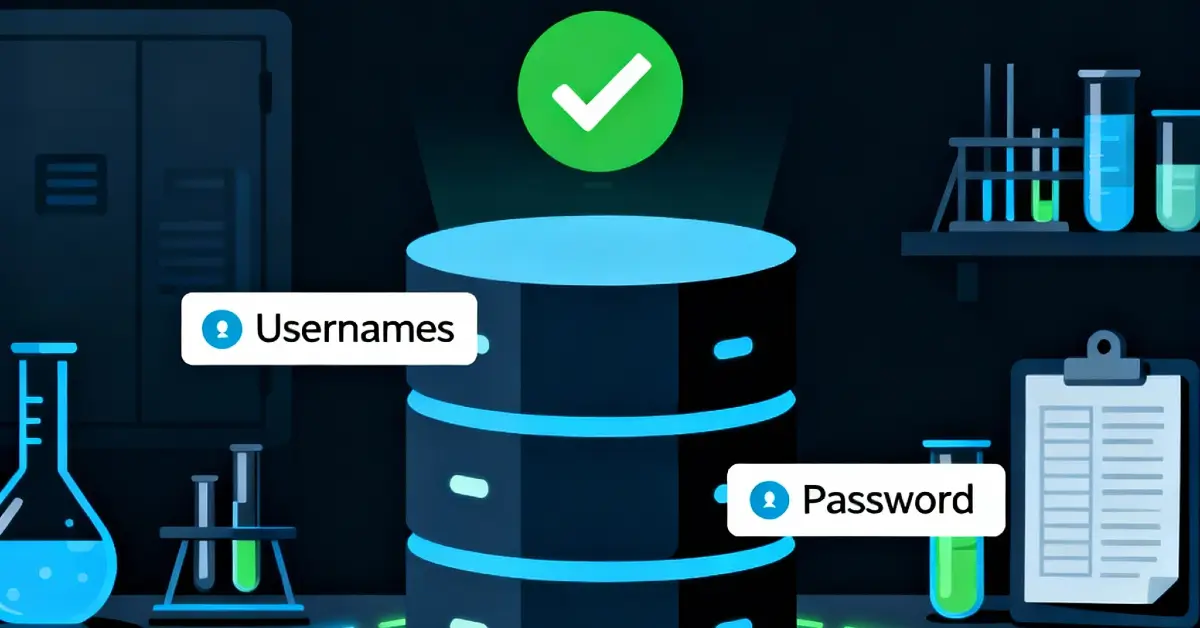
IDOR vulnerabilities often lead to:
- Unauthorized data access (PII leaks)
- Account takeover
- Financial fraud
- Privacy violations
- Regulatory issues (GDPR, HIPAA, etc.)
And unlike many other bugs:
- They are easy to exploit
- They are hard to detect with scanners
- They often affect core business logic
That’s why IDOR consistently appears in the OWASP Top 10 under Broken Access Control.
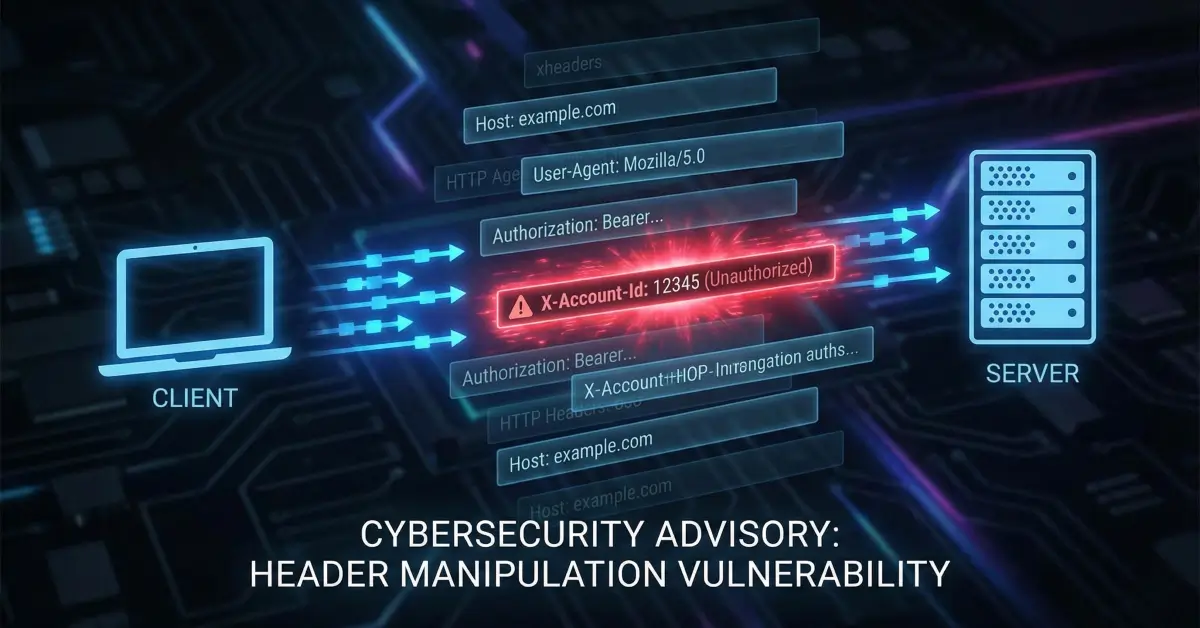
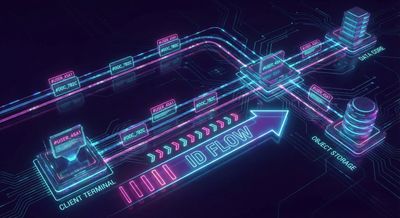
Step 1: Map the Application and Identify Object References
Before manipulating anything, you need visibility.
Browse the application normally, while intercepting traffic using tools like:
- Burp Suite
- OWASP ZAP
- Browser DevTools (Network tab)
Your goal is to identify where object references appear.
Common Object Reference Types
Watch for these in URLs, parameters, headers, and request bodies:
-
Numeric IDs
user_id=1001order=56789
-
UUIDs / GUIDs
docId=550e8400-e29b-41d4-a716-446655440000
-
Usernames or emails
username=johndoeemail=user@example.com
-
Filenames or paths
file=invoice_2024.pdf
-
Encoded or hashed values
id=MTAwMQ==key=5d41402abc4b2a76b9719d911017c592
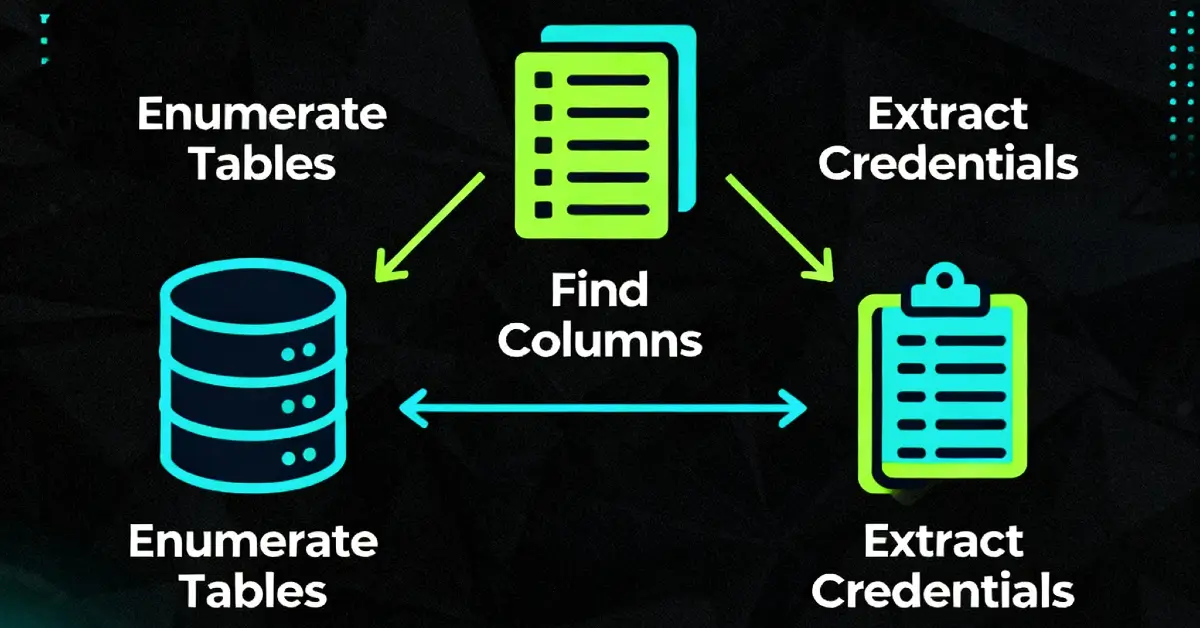
High-Value Endpoints to Focus On
Some endpoints are statistically more likely to contain IDOR flaws:
/api/users/{id}/api/v1/profile/download?file=.../api/orders/history/api/subscriptions/settings/update
At this stage, do not attack. Just observe and document.
Step 2: Manipulate Object References
Once you’ve identified references, it’s time to test authorization.
There are two main IDOR categories.
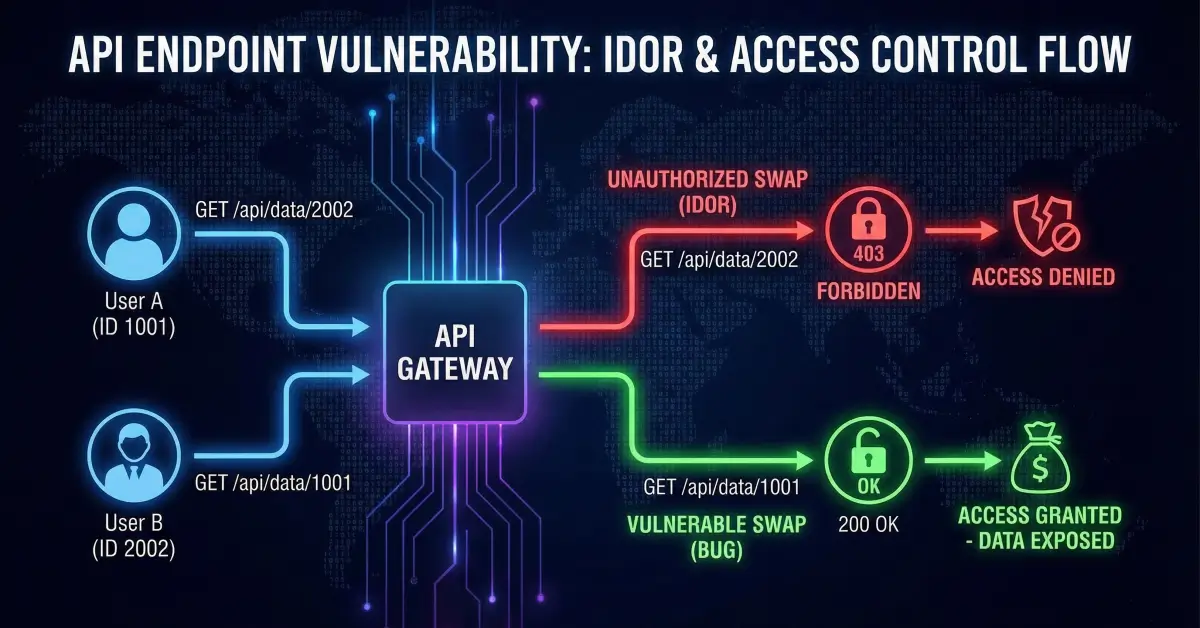
Horizontal Privilege Escalation
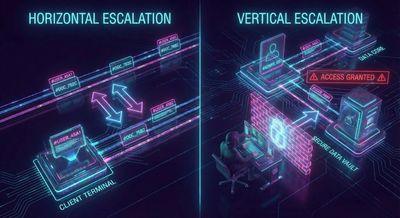
This is the most common IDOR scenario.
You access another user’s data at the same privilege level.
Example
You are logged in as user 1001.
You intercept:
Now change it to:
If the response returns user 1002’s data, you’ve found an IDOR.
This applies to:
- Profiles
- Orders
- Messages
- Uploaded files
Vertical Privilege Escalation
Here, a lower-privileged user accesses higher-privileged functionality.
Common Tests
- Change
role=user→role=admin - Access
/adminendpoints as a normal user - Modify project ownership or permissions
Example
Try:
User ID 1 is often an admin or system account.
Step 3: Test State-Changing Requests (Critical)
This is where IDOR turns critical.
Many testers stop at data exposure. Don’t.
IDOR is far more dangerous when it allows modification.
Requests to Prioritize
- POST
- PUT
- PATCH
- DELETE
Example: Profile Update
Intercept:
Modify:
If user 1002’s email changes, this is a high-impact IDOR.
The same applies to:
- Password resets
- Subscription changes
- Account deactivation
- Permission updates

Step 4: Understand Encoding, Hashes, and Obfuscation
Applications often try to “hide” IDs instead of securing them.
That doesn’t work.
Base64 Encoding
If you see something like:
Always decode it.
Now try encoding other values.
Hashes (MD5, SHA1, etc.)
If an app uses:
Try hashing other IDs locally and swapping them in.
If the server only checks format, not authorization, it’s vulnerable.
“Complex” Identifiers
Even UUIDs can be abused:
- Are they reused elsewhere?
- Do they appear in emails or logs?
- Can they be inferred via other endpoints?
Never assume randomness equals security.
A Practical IDOR Testing Workflow
Let’s put it all together.
Scenario: Social Media App
-
Create two accounts
AttackUserVictimUser
-
Log in as
AttackUser -
Intercept traffic and note requests:
- Modify identifiers:
If VictimUser’s profile loads - IDOR confirmed.
- Test modifications:
If the bio updates, impact escalates from read to write.
Legal and Ethical Reminder
This methodology must only be used on:
- Applications you own
- Explicitly authorized penetration tests
- Bug bounty programs with clear scope
Never test random websites.
Ethical testing protects users - reckless testing harms them.
Key Takeaways
- IDOR is about authorization, not identifiers
- Always test write actions, not just reads
- Encoding and hashing do not equal security
- Logic bugs require logic thinking
- Manual testing beats automation for IDOR
Conclusion
IDOR vulnerabilities don’t require exotic exploits or deep technical tricks. They require attention, curiosity, and a structured mindset.
If you can understand how an application maps users to objects, you can find IDORs.
And if you can find IDORs, you can find some of the highest-impact bugs in real-world applications.
Happy hacking - responsibly.