
React2Shell Explained: Understanding CVE-2025-55182 & CVE-2025-66478 in React Server Components
A clear, accurate, and developer-friendly deep dive into the React2Shell vulnerability (CVE-2025-55182 / CVE-2025-66478), how it works, what is confirmed, what remains theoretical, and how teams can mitigate risk safely.
Disclaimer
This article is for educational and defensive purposes only. It explains a publicly disclosed vulnerability to help teams understand, assess, and mitigate risk. No executable exploit details or harmful instructions are included.
Introduction
On December 3, 2025, the React team published a coordinated security advisory addressing a critical vulnerability in React Server Components (RSC). The issue, cataloged as CVE-2025-55182, affects several packages used in React-powered server environments. Around the same time, the Next.js ecosystem published a related advisory (CVE-2025-66478), which industry tracking later classified as a duplicate of the React CVE.
This vulnerability quickly gained the informal name React2Shell, a label popularized by security researchers to describe its potential impact. At its core, the issue stems from unsafe deserialization of RSC payloads - a condition in which specially crafted data might cause React to interpret untrusted content as structured server metadata.
While much discussion online leaned toward dramatic terminology, official sources remain careful and measured. Many advisories emphasize potential for remote code execution (RCE) under specific conditions, yet also note that misleading or invalid proofs-of-concept were circulating, and that confirmed successful exploitation had not been broadly documented during the early advisory window.
This article walks through what is confirmed, what is not fully confirmed, and what engineering teams should do to secure their applications - all without speculation.
Understanding the Vulnerability
React Server Components (RSC) rely on a serialized protocol sometimes referred to informally as the “RSC Flight protocol.” It allows the server to send structured information to the client in a controlled format. This mechanism is powerful, but it also means that the server must deserialize structured data carefully.
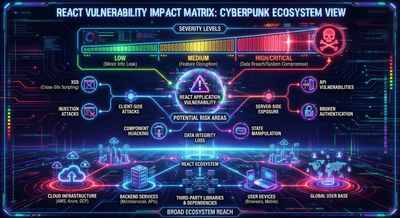
The React advisory identifies that certain affected packages:
- react-server-dom-webpack
- react-server-dom-parcel
- react-server-dom-turbopack
performed unsafe deserialization under certain conditions.
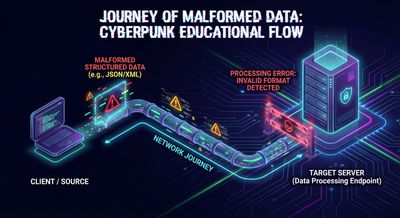
Unsafe deserialization vulnerabilities occur when data supplied to a server is processed as though it were trusted internal metadata. When this happens, an attacker may be able to craft input that influences server behavior in unexpected ways.
What official advisories confirm
- The vulnerability allows potential arbitrary code execution in affected versions.
- The attack surface is unauthenticated, meaning a publicly reachable endpoint that processes RSC payloads could be at risk.
- The vulnerability is rated CVSS 10.0, the highest severity level.
- React released patched versions the same day: 19.0.1, 19.1.2, 19.2.1.
What is not confirmed
- There is no verified public disclosure of attackers successfully reaching internal modules or performing specific environment-secret extraction via this vulnerability.
- There is no confirmed case of supply-chain modification or persistent build tampering linked to React2Shell.
- Several security vendors emphasize that early PoCs were fake or oversimplified, highlighting confusion in the community.
What is widely reported and aligned
Multiple independent vendors (cloud providers, SIEM vendors, research groups) report:
- Exploit attempts and scanning activity appeared shortly after disclosure.
- Attack patterns focusing on structured RSC payloads were observed.
- Organizations are urged to patch immediately and consider this a high-risk issue due to how widespread RSC usage is.
The vulnerability should therefore be taken seriously - but represented accurately.
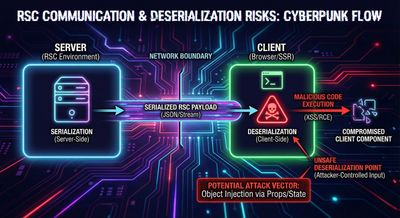
Why React Server Components became the focal point
RSC enables React apps to offload work to the server while shipping minimal JavaScript to the client. To do this, frameworks exchange structured metadata describing:
- Components
- Props
- Bound server functions
- Streaming updates
This metadata is serialized and deserialized frequently. Any weakness in this boundary becomes high-impact.
React2Shell illustrates this structural reality: serialization layers must treat all untrusted input as untrusted, even when dealing with internal component references.
How unsafe deserialization fits into the picture
Below is a safe, non-exploit illustration of what an RSC metadata token might look like:
The vulnerability existed because certain RSC server-side handlers:
- Did not sufficiently validate that incoming structured data was trustworthy.
- Accepted, under some conditions, deserialization patterns that could cause internal logic to process attacker-controlled content.
This type of issue is conceptually similar to many deserialization vulnerabilities across programming ecosystems.
Why unsafe deserialization is dangerous
When a server interprets structured data without enforcing strict validation, an attacker may be able to:
- Influence code paths
- Trigger unintended functions
- Cause internal misrouting of metadata
- Possibly reach a state where arbitrary code execution becomes feasible
This explains why the CVE was scored so high, even without confirmed exploitation.
Affected Versions and Patch Guidance
According to the React advisory:
Affected React packages
- react-server-dom-webpack
- react-server-dom-parcel
- react-server-dom-turbopack
Vulnerable versions include:
- 19.0.0
- 19.1.0
- 19.1.1
- 19.2.0
Patched versions:
- 19.0.1
- 19.1.2
- 19.2.1
Official guidance recommends:
Upgrade immediately to the nearest patched version.
What about Next.js?
Next.js published its own CVE (CVE-2025-66478), which industry trackers now treat as a duplicate of CVE-2025-55182. The vulnerability ultimately originates in the React RSC packages, not in Next.js itself.
Next.js users should:
- Ensure they run a patched React version.
- Redeploy applications so that patched packages take effect.
- Verify serverless/edge runtimes also refreshed cached layers.
How exploitation might occur (high-level, theoretical only)
To maintain AdSense safety and avoid providing harmful guidance, the following explanation describes only the conceptual direction of exploitation - not a payload, not a technique, and not actionable details.
A possible exploitation sequence could look like this:
- An attacker identifies an endpoint that accepts or passes through structured RSC data.
- The attacker supplies specially shaped data that resembles internal metadata.
- An affected server interprets this data during deserialization.
- Under vulnerable versions, this may lead to unsafe behavior.
- Arbitrary code execution becomes theoretically possible.
This is similar to how many major deserialization vulnerabilities behave across languages - it is not unique to React.
What is confirmed
- Arbitrary code execution is a documented possible outcome under vulnerable versions.
What is not confirmed
- There is no public, validated evidence of real-world attackers achieving RCE in major production deployments using this vulnerability as of this writing.
- Claims about internal module abuse, environment secret extraction, or persistent build modification remain theoretical risks, not confirmed events.
Maintaining a clear boundary between “possible” and “confirmed” is critical for credibility and safety.
Risk Context: Why This Matters Even Without Confirmed Breaches
Organizations treat this as an urgent security event because:
- React Server Components are widely deployed.
- Many production servers process RSC payloads by default.
- The vulnerability is triggered pre-authentication.
- A CVSS 10.0 score indicates worst-case potential impact.
In incident response, “no confirmed breaches yet” does not reduce the priority of remediation when official assessments show that unsafe deserialization may enable RCE.
Safe Example: Recognizing Metadata-Like Payloads
Below is a safe, sanitized, educational example of content that resembles structured metadata a server may need to validate.
This is not reflective of any exploit; it simply illustrates the shape of content that a framework might parse.
The key lesson is:
Any input that is structured, nested, or serialized should be validated as if it came from an untrusted source.
How Organizations Should Mitigate Risk
Below are general-purpose defensive measures aligned with React's advisory and common industry practice.
1. Patch immediately
This is the only definitive mitigation. Any system running vulnerable RSC packages should upgrade to:
- 19.0.1, 19.1.2, or 19.2.1
2. Redeploy and clear stale layers
Some environments cache Node layers or serverless runtimes. A redeploy ensures patched packages propagate.
3. Validate serialization boundaries
Even after patching:
- Treat all data inputs as untrusted.
- Enforce strict schema validation.
- Avoid automatic deserialization unless the format is validated.
Serialization boundaries are one of the most common root causes of high-severity vulnerabilities.
4. Review logging around RSC endpoints
Look for:
- Unexpected shapes in request bodies
- Large or deeply nested objects
- Requests during the patch-window related to RSC paths
5. Harden CI/CD pipelines (precautionary)
While there are no confirmed reports of supply-chain intrusion, CI hardening is widely recommended in any deserialization incident.
Measures include:
- Using ephemeral build agents
- Verifying checksums
- Minimizing privileges during builds
- Enforcing dependency auditing
These steps help reduce the blast radius of any future serialization-related issue.
What This Teaches About Secure Application Design
React2Shell reminds us of a broader engineering truth:
Whenever systems deserialize structured data, they must enforce trust boundaries explicitly.
Lessons organizations can apply anywhere
- Never assume serialized metadata is safe.
- Always validate object shapes and fields.
- Explicit allowlists are safer than deny-lists.
- Auto-resolving identifiers should be tightly restricted.
- Framework convenience features must be paired with security review.
Serialization issues recur across:
- Java
- Python
- Node.js
- PHP
- Ruby
- Cloud function runtimes
React2Shell is another example of why serialization boundaries require deep attention.
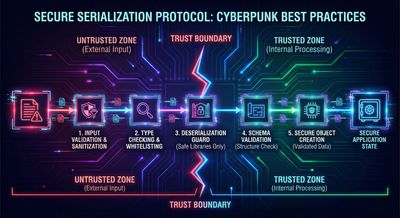
Table: Confirmed Facts vs Theoretical Risks
| Topic | Confirmed by official advisories | Theoretical / Risk-based (not confirmed) |
|---|---|---|
| Vulnerability enables potential RCE | ✔ Yes | - |
| CVSS 10.0 severity | ✔ Yes | - |
| Unsafe deserialization root cause | ✔ Yes | - |
| Exploit attempts observed (scanning) | ✔ Yes (multiple vendors) | - |
| Successful real-world RCE events | ❌ Not confirmed | ⚠ Possible in theory |
| Supply-chain modification via this flaw | ❌ Not confirmed | ⚠ Discussed as theoretical risk |
| Internal module or secret extraction | ❌ Not confirmed | ⚠ Theoretical worst-case scenario |
This separation maintains accuracy while still conveying legitimate security stakes.
Final Thoughts
CVE-2025-55182 (React2Shell) will be remembered as one of the most significant JavaScript-ecosystem vulnerabilities of its year. Not because of confirmed large-scale exploitation, but because of how broadly the affected code is deployed and how deeply it touches the serialization model powering modern server-driven React applications.
Advisories from the React team, Next.js maintainers, cloud vendors, and multiple security research groups reach the same fundamental conclusion:
- Patch immediately
- Validate untrusted input
- Review your serialization boundaries
- Strengthen CI/CD integrity
Strong engineering hygiene - and quick adoption of patched versions - ensures systems remain safe not only from this vulnerability, but from future serialization issues as well.
References
- React Security Advisory - CVE-2025-55182 (Dec 3, 2025)
- Carnegie Mellon CERT Notes on CVE-2025-55182
- Unit 42 Sector Analysis
- Radware Statement Regarding Misleading PoCs
- Next.js Advisory (CVE-2025-66478)
- Multiple cloud provider threat-intelligence notices










