$1,000 Bounty for a 403 Bypass: Lessons from a Subtle but Powerful Discovery
How a researcher turned a simple 403 Forbidden response into a $1,000 bounty by exploiting an HTTP method logic flaw - and what every bug hunter can learn from it.
Disclaimer: This write-up is based on another security researcher’s public bug bounty finding.
The content is shared for educational and awareness purposes only.
The goal is to help developers and ethical hackers understand how subtle HTTP logic flaws can lead to unauthorized access and how to defend against them.
🚀 Introduction: When “Forbidden” Isn’t Really Forbidden
In the world of bug bounty hunting, not every vulnerability hides behind a flashy exploit or fancy payload.
Sometimes, the biggest wins come from quiet logic bugs - the kind that slip through automated scanners and live unnoticed in plain sight.
This is one such case:
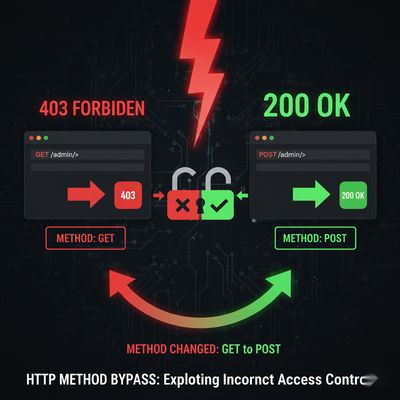
A researcher earned $1,000 by discovering that a simple HTTP method change turned a 403 Forbidden into a 200 OK, unlocking restricted admin routes in a production web application.
No advanced tools.
No zero-days.
Just persistence, pattern recognition, and an understanding of how servers handle different request methods.
This is the story - and the lesson - behind that discovery.
🧭 Laying the Groundwork: From Curiosity to Commitment
Like most beginners, the researcher didn’t start with a complex setup or elite automation.
They began with curiosity - reading HackerOne reports, analyzing write-ups, and understanding what separates good hunters from great ones.
They spent weeks learning how:
- Web apps handle input and routing
- Permissions are enforced (or not)
- Recon and logic testing complement automated scans
After gaining some comfort with tools like Burp Suite, curl, and HackerOne’s program listings, they picked a target - an established application we'll call TargetApp.
The motivation wasn’t to find an easy bug, but to observe how a hardened app behaves under real-world conditions.
🔍 Early Exploration: The Quiet Before the Breakthrough
Recon began with simple, systematic steps:
- Browsing manually to understand user flows.
- Reviewing
robots.txtto see disallowed or sensitive directories. - Testing classic vectors - XSS, IDORs, open redirects, parameter tampering.
- Capturing traffic in Burp Suite for behavioral patterns.
Weeks passed - nothing substantial surfaced.
The app seemed bulletproof. Strong responses, consistent status codes, strict redirects, and almost no obvious vulnerabilities.
It was a typical "quiet phase" every hunter experiences: the long stretch before something finally clicks.
💡 The Breakthrough: Re-reading robots.txt
Frustrated but not defeated, the researcher decided to review earlier notes.
They revisited every small lead - including a simple file that many hunters overlook after the first scan: robots.txt.
Inside it, one line stood out:
Not unusual - plenty of websites disallow admin paths from search engine indexing.
But what made this interesting was how consistent the developer naming was.
“/admin/” was real, not random - meaning it might correspond to a live endpoint.
Time to test it.
They intercepted a request to /admin/ in Burp Suite.
The server’s response?
A 403 means the server knows the resource exists - it’s just not allowing access.
That small hint was enough to keep digging.

🧠 The Method Bypass: Turning 403 into 200
Instead of giving up, the researcher started running through a 403 bypass checklist - a collection of low-effort, high-yield tricks that often expose overlooked logic flaws.
Common bypass attempts included:
- Modifying request headers (
X-Forwarded-For,Referer,Origin, etc.) - Adding special characters or encodings (
/admin/.,/admin/%2e/) - Switching between HTTP methods (GET, POST, PUT, HEAD, etc.)
And it was that last trick that changed everything.
They modified the intercepted request in Burp Suite:
and simply changed it to:
Then hit Forward.
The response?
Forbidden no more.
The /admin/ dashboard was accessible.
🧩 Expanding the Discovery
Curious, the researcher tried the same trick on similar routes:
/admin/users/admin/config/admin/logs
Each of these 403 routes became accessible when the request method switched from GET to POST.
That confirmed the issue wasn’t a fluke - it was a systemic authorization flaw affecting all admin endpoints.
No further exploitation was needed. The bug was clear, reproducible, and impactful.
📝 The Report: From Burp Suite to $1,000
A good bug is only as valuable as its report.
The researcher carefully documented everything:
- ✅ Summary of the issue
- ✅ Affected endpoints
- ✅ Step-by-step reproduction (including HTTP requests and responses)
- ✅ Proof-of-concept screenshots from Burp Suite
- ✅ Suggested fixes
They submitted the report on HackerOne.
Within days, the triage team responded:
“Issue confirmed. Valid. Impact acknowledged.”
Shortly after, the bounty was awarded: $1,000.
🧰 Why This Bug Worked: A Deep Dive
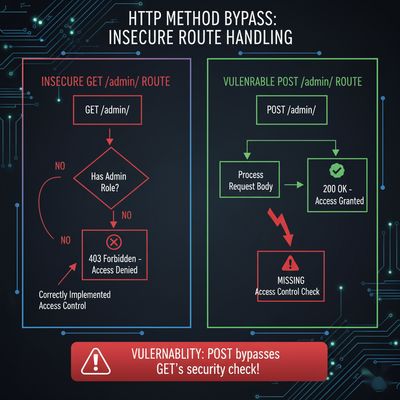
At the core, this was a broken access control vulnerability caused by improper method handling.
Here’s what likely happened under the hood:
- The backend had strict access control for GET requests but not for POST.
- Security middleware checked authorization only for certain methods.
- The
/admin/endpoints validated permissions inconsistently, allowing POST requests through.
This kind of vulnerability usually appears when:
- APIs evolve without uniform access rules.
- Developers assume “POST = authenticated form submission.”
- Web servers or frameworks misapply route filters.
Example (Simplified):
The developer assumed POST wouldn’t be used manually - but attackers think differently.
🔒 Impact Analysis: Why This Was Worth $1,000
This wasn’t just a minor logic oversight.
It effectively allowed unauthenticated users (or low-privileged users) to access restricted admin pages.
Potential Risks:
- Disclosure of internal configuration details.
- Unauthorized access to admin panels or dashboards.
- Exposure of sensitive API responses.
- Potential privilege escalation if chained with another flaw.
Even without data modification, viewing restricted areas is enough to justify a high-severity rating - especially on production systems.
💡 Lessons Learned
1. Revisit and Reobserve
The winning clue came from re-reading robots.txt.
The same file that looked boring a month earlier became the key to the $1,000 discovery.
Sometimes, the vulnerability isn’t in new data - it’s in old data seen with new eyes.
2. Method Matters
Changing HTTP methods is a low-effort test that many skip.
Remember: 403 doesn’t mean “impossible,” it means “interesting.”
3. Manual Testing > Automation
No scanner will think to “try POST instead of GET.”
That’s a human insight - and why manual testing remains unbeatable for logic flaws.
4. Consistency Wins
Two months of quiet effort led to one lucky observation.
Persistence is the real skill behind every payout.
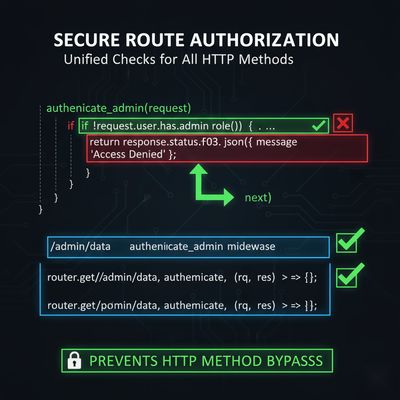
🧩 Defensive Take: Fixing the Root Cause
For developers, preventing this issue is straightforward but essential.
Developer Checklist:
| Category | Mistake | Solution |
|---|---|---|
| Authorization | Access control tied only to GET | Apply authorization checks for all methods |
| Middleware | Inconsistent validation filters | Use global security middleware |
| Code Design | Duplicate route definitions | Merge routes and enforce common checks |
| Testing | No manual 403 validation tests | Add regression tests for multi-method access |
🧠 The Bigger Lesson: Patience Pays More Than Tools
This story isn’t just about a $1,000 bounty - it’s a reminder that focus and consistency beat brute force.
While others ran heavy scanners, this researcher slowed down, revisited notes, and noticed a single forgotten pattern.
In bug bounty hunting, success often comes from looking twice at the things everyone else overlooks once.

References
- OWASP API Security Top 10 - Broken Function Level Authorization
- HackerOne: 403 Bypass Reports
- PortSwigger: Access Control Vulnerabilities
- Bugcrowd University: Logic Flaws 101
Published on herish.me - real stories, real bugs, real lessons from the frontlines of ethical hacking.