From 403 to Fortune: How an Access Control Bypass Turned a 403 into Admin Access
A detailed, defensive write-up of an access-control bypass: 403 bypass techniques, parameter pollution, method tampering, JWT manipulation, PoC and mitigations.
Disclaimer (educational & defensive only)
This article summarises an anonymized finding reported by another security researcher. It explains techniques used to identify and validate authorization weaknesses and provides comprehensive defensive guidance. Do not test or exploit third-party systems without explicit written permission.
A simple 403 Forbidden should be the end of the story: access denied, move on. But in real-world apps, 403 is sometimes the start of a chain of subtle misconfigurations that-when combined-become a full access-control bypass. The researcher behind this write-up methodically combined multiple techniques (method tampering, header injection, parameter pollution, URL encoding tricks and JWT manipulations) and built a PoC that turned a blocked admin panel into a successful 200 OK with admin data.
This article turns that write-up into a long-form defensive guide: what was discovered, how it was validated (lab-safe PoCs), why it matters, and - most importantly - how engineering teams can detect and fix these classes of problems.
TL;DR (one-paragraph summary)
A researcher encountered GET /admin returning 403. By enumerating method variations, injecting headers (notably X-Forwarded-For: 127.0.0.1), polluting parameters (duplicate role values), using URL-encoding and Unicode normalization tricks, and finally manipulating JWT payloads, they combined multiple weaknesses and bypassed server-side authorization checks. The final chain used encoded path traversal + headers + parameter pollution and returned 200 OK with admin-level data. The issue highlights the importance of canonicalization, strict header handling, parameter parsing consistency, and robust token verification.
Why 403 is not always safety
Many teams believe a 403 proves “we blocked unauthorized access”. In practice the 403 response is only as reliable as:
- the consistency of request parsing across routing layers (web server, reverse proxy, app),
- canonicalization (path normalization across layers),
- header handling (which component trusts and uses headers like
X-Forwarded-For), - parameter parsing (how duplicates or mixed sources are resolved),
- and token validation (JWT verification and algorithm enforcement).
Attackers chain tiny inconsistencies into reliable bypasses. The researcher's path demonstrates this precisely.
Recon & methodology (how they approached testing)
The researcher followed a systematic methodology:
- Ground truth - visit the admin route and confirm
403. - Method fuzzing - try other HTTP verbs (
POST,PUT,PATCH,HEAD,OPTIONS) to see if authorization is method-dependent. - Header injections - send headers commonly trusted by internal routing (e.g.,
X-Forwarded-For: 127.0.0.1,X-Original-URL) to observe differences. - Parameter pollution - send duplicated parameters in query/body (e.g.,
role=user&role=admin) and mixed encodings. - Path normalization - craft encoded/Unicode variants of path segments (
%61dmin, unicode lookalikes) to bypass naive string checks. - Token fuzzing - decode and test JWT handling (algorithm confusion, duplicate claims).
- Combine techniques - systematically merge promising tricks to find a chain that yields
200 OK.
This stepwise approach is repeatable and effective for logical authorization flaws.
Key techniques that worked (explained)
Below are the main techniques the researcher used, with concise rationale.
1. HTTP method fuzzing
Some applications implement authorization per-method (e.g., GET blocked, POST allowed) either accidentally or due to legacy route wiring. Trying all standard HTTP methods can reveal such inconsistencies.
If one method returns 200 while others 403, investigate method-specific middleware or routing rules.
2. Header injection & trust assumptions
Reverse proxies and WAFs often set or rely on headers like X-Forwarded-For, X-Original-URL or X-Rewrite-URL. If the application trusts these headers without validating them (or if an upstream component incorrectly trusts them), an attacker can influence internal logic.
Example headers tested:
If the app uses X-Forwarded-For to allow "internal" traffic, forging 127.0.0.1 can bypass internal-only checks.
3. Parameter pollution (duplicate keys)
Different frameworks and parsers resolve duplicated parameters differently. Sending role=user&role=admin may cause the server to use the last, first, or an array-leading to ambiguity.
Examples:
If one parser treats multiple role fields inconsistently across modules (auth vs data access), an attacker can force an admin role to be considered.
4. URL encoding & unicode normalization
Applications may canonicalize paths differently across webserver, proxy, and app. Using encoded bytes or Unicode lookalikes (Cyrillic а vs Latin a) can evade naive string checks.
Examples tried by the researcher:
Normalization inconsistencies are especially dangerous when combined with path traversal attempts.
5. JWT manipulation (algorithm confusion & duplicate claims)
JWTs must be validated correctly. The researcher tried:
- decoding tokens with signature verification disabled to inspect claims,
- building tokens with
alg: noneto test algorithm acceptance, - sending duplicate
roleclaims in payload to exploit claim parsing inconsistencies.
Poisoning the token payload or exploiting algorithm acceptance can change the effective role value.
Important: modern libraries and frameworks should never accept alg: none or treat duplicate claims ambiguously.
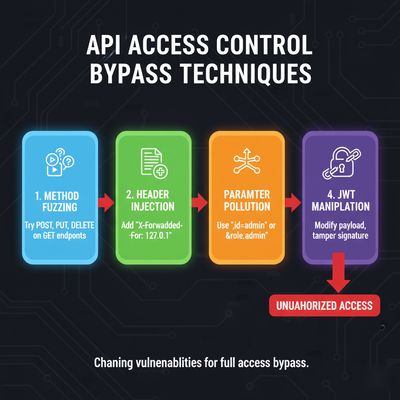
The PoC chain (how the pieces combined)
Individually, each trick was a partial signal. The breakthrough came when multiple layers were combined:
- Path normalization trick produced an alternate path that bypassed an early router check.
- Header injection (
X-Forwarded-For: 127.0.0.1) flagged the request as internal to a downstream component. - Parameter pollution sent a duplicate
rolevalue that later modules parsed asadmin. - A different HTTP method (e.g.,
PUT) triggered a code path that trusted theroleheader more than the token.
The final request looked conceptually like this (PoC conceptual example - do not run against third-party systems):
This resulted in 200 OK and a payload containing admin-level data.

Full PoC automation (lab-safe conceptual script)
The researcher used an automation harness to generate combinations. Below is a sanitized lab-only template showing the idea of method, header and path fuzzing. Use only in authorized test environments.
Impact assessment
If an adversary can reliably turn 403 into 200 for admin endpoints, consequences include:
- Full data exposure (user lists, financials, PII).
- Privilege escalation and account takeover.
- Creation of admin accounts, deletion of data, or execution of admin actions.
- Lateral movement inside internal APIs that assume "admin only" routes are protected.
- Audit/logging gaps because the bypass may circumvent enforcement layers.
The business, compliance and legal impact is severe.
Root causes & systemic failures
This issue is rarely a single bug - it's a stack problem:
- mixed parsing behavior across components (proxy vs app),
- unsafe assumptions about trusted headers,
- duplicated code paths with inconsistent authorization enforcement,
- weak token validation and acceptance of unsafe JWT algorithms,
- lack of canonicalization and normalization across routing layers.
Fixes must be both tactical (fix the endpoint) and strategic (remove implicit trust and unify canonicalization).
Remediation checklist (engineer-focused)
-
Canonicalize and normalize early
- Normalize request path and parameters at the earliest entry (reverse proxy or gateway) and pass canonical form downstream.
-
Reject untrusted headers from the public internet
- Strip or ignore
X-Forwarded-*,X-Original-URLand related headers at the edge unless they are set by a trusted reverse proxy. Validate their origin.
- Strip or ignore
-
Consistent authorization middleware
- Centralize authorization logic into a single middleware invoked by all methods and routes. Don't rely on ad-hoc route-level checks.
-
Parameter handling consistency
- Use consistent parameter parsing library across all components. Reject duplicate parameter keys or explicitly define policy (first wins/last wins) and enforce it.
-
Path normalization & encoding defenses
- Normalize encoding forms and Unicode to NFC (or your chosen form) and block suspicious encodings. Validate against a canonical whitelist of allowed paths.
-
JWT validation best practices
- Verify signatures with robust libraries, disallow
alg: none, checkexp/nbf/iat, and validate expected claims. Reject tokens with duplicate claims.
- Verify signatures with robust libraries, disallow
-
Method-level access control
- Apply the same strict authorization policy to all HTTP methods on a route; explicitly deny unsupported methods.
-
Secure logging and monitoring
- Log denied requests with paths, headers and tokens (sanitised), and monitor for spikes in failed/alternative-method access.
-
Testing & CI checks
- Add automated tests for header spoofing, parameter pollution, encoded path variants, and algorithm confusion attempts in CI.
-
Least privilege & fail-safe defaults
- Default to deny. If authorization state is ambiguous, return
403and alert.

Detection & monitoring guidance
- Alert on any
200responses to admin endpoints from unusual IPs or using uncommon methods. - Detect repeated attempts to mix
roleparameters or multiple values for the same param. - Monitor for unusual header combinations (
X-Forwarded-For: 127.0.0.1from external IPs). - Use fuzzing in staging to exercise parameter-pollution and path-encoding cases regularly.
Responsible disclosure & triage notes
If you are a researcher:
- Stop active exploitation when you have a reliable PoC.
- Share a minimal, reproducible lab-safe test with the vendor (redact production data).
- Provide impact scenarios and recommendations - help teams fix correctly.
- Cooperate on verification and avoid public disclosure until fixed.
If you are a vendor triaging such reports:
- Verify the PoC in a staging environment mirroring production routing and proxies.
- Patch canonicalization, header handling and centralize auth logic before rolling to prod.
- Consider rotating keys/tokens and rebooting certs only if tokens are suspected compromised.
Final thoughts
Authorization failures rarely live alone. They are often the result of small inconsistencies across application stacks. The safe approach is to eliminate assumptions-strip untrusted headers, canonicalize early, centralize authorization, treat duplicated parameters as suspicious, and validate tokens robustly.
A 403 should be a clear stop sign, not an invitation to "try harder." Defensive engineering, consistent parsing, and layered checks are the best way to keep 403 meaningfully final.
Appendix - quick checklist for incident response
- Reproduce in staging with canonicalized proxy configuration.
- Temporarily block risky endpoints from public internet while patching.
- Rotate any exposed credentials if there is evidence of data exfiltration.
- Add dedicated tests for header spoofing and parameter pollution to CI.
- Share a post-mortem: list affected endpoints, mitigation steps and timelines.