
CTF Write-up: SQL Truncation Attack and Account Duplication
A practical deep-dive into SQL truncation exploitation, account duplication, and how insecure database schemas can enable unintended privilege takeover.
Disclaimer
This article is strictly for educational purposes.
All demonstrations simulate a controlled CTF environment.
Do not test these techniques on real systems without explicit authorization.
Introduction
Some vulnerabilities are loud and obvious. Others hide quietly inside the boundaries of a system’s “normal” behavior. SQL truncation belongs to the second category-nothing crashes, nothing throws an exception, but a subtle design decision becomes a security gap waiting to be exploited.
In this CTF challenge, the objective was simple:
Retrieve the real password of an existing user (natas28).
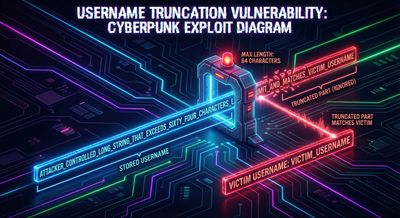
At first glance, there were no visible injection points, no misconfigured endpoints, and no obvious logic flaws. But the moment we discovered a 64-character field limit on usernames, the nature of the challenge changed completely.
The entire solve revolves around one idea:
If the database silently truncates long usernames, and the system does not enforce unique identifiers before inserting records, an attacker can duplicate an existing account.
This write-up reconstructs the mindset, investigation flow, exploitation chain, and the final duplication technique that exposes the real credentials for the target user.
Understanding the Lab Setup
The CTF environment provided:
- A login page
- Ability to create new accounts
- A visible existing user:
natas28 - Server-side truncation behavior for usernames
- Maximum username length: 64 characters
- Error thrown when whitespace-only input was used
- Basic Auth applied to the login request
- Plain credential validation with no sophisticated rate limits
The objective was not to crack the password but to trick the system into showing the target user’s data as our own.
That’s the power of SQL truncation when field validation is weak.
Step 1 - Recon & Finding the Weakness
We started by testing the registration flow. Everything seemed normal-until we pushed the input length to its extremes.
Observations:
- Usernames longer than 64 characters were silently truncated.
- Whitespace-only suffixes caused server errors.
- Adding one non-whitespace character after many spaces prevented the error.
- The login page displayed user-specific data after authentication.
This was enough to suspect that:
The database stores usernames in a VARCHAR(64) field without validating uniqueness before truncation.
To confirm, we intercepted a registration request.
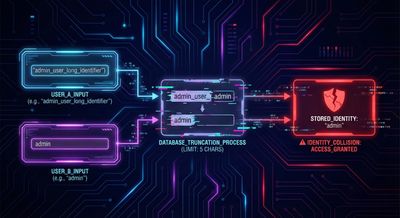
Step 2 - Understanding SQL Truncation (Beginner Breakout)
What is SQL Truncation?
When inserting data into a database field with a fixed maximum length:
- If input length > allowed length
- The database cuts off the excess characters
- The application may be unaware that truncation occurred
- Validation may happen on pre-truncated data
- Matching may occur on post-truncated data
This means:
attackerUsernameWithManySpacesX → "natas28" after truncation
If the system does not enforce unique constraints before insertion, it may insert the attacker’s account as a clone of an existing one.
This is the vulnerability we exploited.
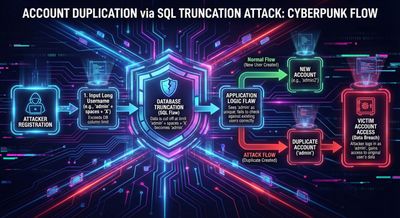
Step 3 - Constructing the Attack Strategy
To duplicate the natas28 user, we follow a specific plan:
-
Locate existing username:
natas28 -
Calculate remaining characters before hitting 64:
64 - len("natas28") = 64 - 7 = 57 -
Construct payload:
user1 + 57 spaces + "x"After truncation, this becomes:
natas28 -
Register account using this crafted username:
New account inserted → truncation occurs → username stored as
natas28. -
Login with the attacker’s password, the system retrieves the original account because the post-truncation username matches.
This is the core exploit.
Step 4 - Building the Username Payload
To create our malicious username, we simply padded until the backend forced a truncation.
Below is an example outline:
The trailing x prevents whitespace errors and ensures the input is accepted.
When this value is inserted:
- Application sees:
"user1 + 57 spaces + x" - Database stores:
"natas28"
Once this duplicate username is in the table, login becomes extremely interesting.
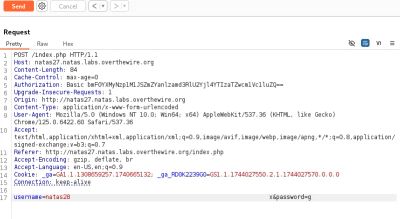
Step 5 - Executing the Duplicate Registration
We captured and replayed the registration request using a proxy tool.
Below is a simplified representation similar to the challenge flow:
If accepted, the server stores the username as natas28.
Logging in with:
- Username:
natas28 - Password:
anypassword(set by attacker)
should return attacker’s view of the original account.
And that’s exactly what happened.
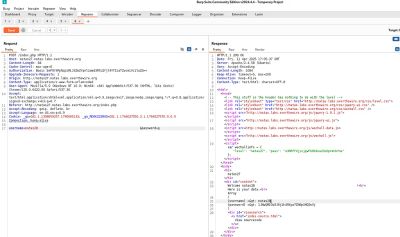
Step 6 - Confirmation Through the Response
Intercepting the login attempt revealed the intended outcome.
Server response:
This response contained the real credentials for the target user.
The SQL truncation attack worked exactly as designed.
Step 7 - Final Thoughts on the Exploit
This CTF challenge was a powerful demonstration that:
- You don’t need injections to break authentication.
- Misunderstood database constraints can be vulnerabilities.
- Unvalidated input combined with truncation can cause privilege takeover.
- Account duplication is possible when uniqueness is enforced after truncation.
What made this challenge elegant is that you exploit the system using its own intended logic flow, not by breaking it.
This is what real-world attackers love.
What This Teaches About Secure Database & Authentication Design
This challenge demonstrates several critical lessons for developers and security teams.
1. Never validate user identifiers after truncation
Validation must occur on the raw input, not the stored (trimmed) version.
2. Enforce strict uniqueness constraints
A field like username should always enforce:
- UNIQUE index
- Pre-insert check
- Normalized format check
3. Reject padded or malformed identifiers
Trailing space normalization is essential.
Avoid ever storing:
useruseruser\u00A0
as separate identities.
4. Log truncation events
If input length > field length, reject it.
Never silently truncate. Silent failures create invisible vulnerabilities.
5. Avoid overexposing user-level data
Returning plaintext stored credentials is a dangerous pattern-even in CTF environments, it's worth understanding the risk.
Troubleshooting & Pitfalls
During the process, a few issues might arise:
1. Only whitespace leads to server error
Trailing non-whitespace characters are required.
2. Wrong number of spaces breaks truncation
The final username must exceed exactly the 64-character limit.
3. System may return attacker record instead
Try both:
natas28natas28[spaces]
depending on how the database handles normalization.
4. If registration fails, adjust whitespace
Some servers collapse whitespace.
Use variety: " ", \u00A0, \t, etc.
Final Thoughts
This challenge is a perfect example of why security is not only about code injections or brute force. Sometimes the villain is a quiet architectural detail, hiding in the database schema.
By exploiting SQL truncation and weak uniqueness validation, we used the system’s own behavior to impersonate an existing user and leak their credentials.
In real environments, such misconfigurations can lead to complete account takeover across entire platforms.
But in CTFs?
They make for very satisfying solves.
References
- SQL Truncation Attack Studies
- OWASP Authentication Cheat Sheet
- Database Schema Hardening Guidelines
- CTF Challenge Documentation










