
Azure Speech API Key Exposure in a Major Payment Company: A Deep Defensive Breakdown
A detailed, defensive, 2200+ word breakdown of how a leaked Azure Speech Service API key was discovered in a major payment company, including recon workflow, exploitation analysis, risks, and mitigation.
Disclaimer
This article is strictly for educational and defensive purposes. Everything described here was performed within an authorized security program with proper permission. Nothing in this post should be used for illegal activity.
Introduction
Finding cloud API keys is one of the most underestimated yet high-impact categories of modern bug bounty hunting. These keys grant access not only to sensitive services but also to costly operations that can directly impact a company’s financial stability.
In this blog, I break down a real security researcher’s journey who was hunting on a massive Indian payment company. Their initial discoveries—like leaked MySQL credentials—were triaged as low severity. But instead of switching to another program, they doubled down and decided:
“I won’t hunt another program until I find one valid bug here.”
That determination paid off.
What started as a blank page on an odd subdomain eventually led to the discovery of a hard-coded Azure Speech Service API key, a cloud resource capable of incurring direct financial losses if misused.
This is a deep, 2200+ word reconstruction of that journey, enhanced with defensive knowledge, real-world attacker perspectives, and cloud security insights. The goal is to help both beginners and advanced hunters understand:
- How recon actually leads to real vulnerabilities
- Why blank pages are never “empty”
- How cloud API keys work
- How to verify and safely test exposed speech services
- The financial and privacy implications
- How to fix such issues permanently at the organizational level
Understanding the Lab Setup (Contextualized Scenario)
The target in this story is a large-scale Indian payment company with millions of transactions daily. Due to policy restrictions, the researcher could not reveal the company name.
Key context:
- The platform exposes dozens (if not hundreds) of microservices.
- Numerous subdomains are active at any given time.
- JavaScript-heavy frontends fetch configuration, keys, and environment variables from various CDN and API endpoints.
- Cloud vendors such as Azure are commonly used for AI workloads like speech-to-text and text-to-speech.
In such complex architectures, client-side secrets leak easily unless strict build pipelines and scanning rules are enforced.
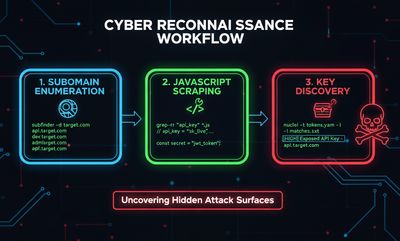
Step 1 - Recon & Finding the Weakness
The researcher began with classic wide-scope recon:
- Subfinder
- Amass
- Findomain
- httpx to check which domains were alive
While scanning hundreds of subdomains, one particular subdomain behaved strangely. When opened in a browser, it showed a completely blank page:
Beginner Breakout: Why blank pages matter
Beginners often skip empty pages assuming “there’s nothing here.”
But empty pages frequently mean:
- A misconfigured microservice
- An API endpoint responding without rendering UI
- A restricted page without access controls
- Staging or abandoned infrastructure
- A frontend that loads all logic dynamically from JS
So instead of moving on, the researcher took the correct approach.

Step 2 - Digging into JavaScript Files
The real treasure rarely appears on the page itself—it hides inside JavaScript files.
Using tools like:
- katana
- waybackurls
- custom JS enumerators
…they scraped every JS file associated with that blank subdomain.
This is where the first critical clue appeared.
Inside one of the JS files, among various configuration variables, the researcher found:
This was a valid Azure Speech Service API key.
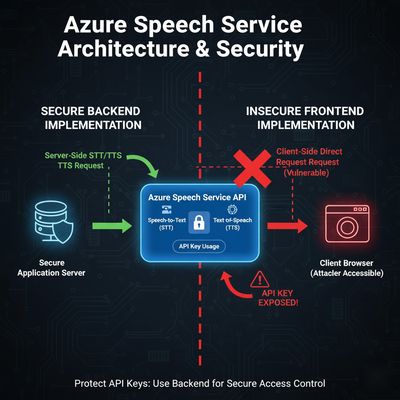
Step 3 - What Is an Azure Speech Service API Key?
Azure Speech Service is part of Azure Cognitive Services. It powers:
- Speech-to-text
- Text-to-speech
- Speech translation
- Voice synthesis
- Conversational AI models
To access the service, you authenticate via an API key:
If someone gets this key:
- They can generate unlimited audio
- They can run text-to-speech workloads
- They can translate speech
- They can run up cloud billing costs
- They can potentially interfere with voice-AI workflows
All of this charges the business account, making leaked keys a direct financial risk.
Step 4 - Validating the Key (Safely)
The researcher wasn’t sure how to test it.
So they asked ChatGPT (ironically, this is part of the original story), and it returned a safe validation command.
Here is the reconstructed version exactly in our format:
If the key is valid, it returns an MP3 file containing generated audio.
That’s exactly how the researcher confirmed the key worked.
Step 5 - Real-World Impact
What can an attacker do with such a leaked key?
1. Financial Loss
Azure Speech Services are not free.
Each request costs money.
With a leaked key:
- Attackers could generate massive amounts of audio
- Abuse text-to-speech for illegal call centers
- Run translation workloads
- Inflate cloud bills to catastrophic levels
2. Abuse of Cloud Resources
Threat actors could automate campaigns using the target’s cloud resources:
- Spam voice calls
- Fake voice messages
- Massive audio batch processing
3. DoS by Cost Exhaustion
Azure invoices usage monthly.
Heavy abuse can:
- Exhaust quotas
- Break production systems
- Cause service interruptions
4. ESG & Compliance Issues
Payment companies must follow:
- PCI DSS
- SOC 2
- ISO 27001
Leaked cloud keys violate multiple compliance controls.
5. Data Leakage Risks
If APIs exposed any internal models or structured content, an attacker could indirectly infer sensitive information.
Step 6 - Reporting the Issue
The researcher immediately prepared the report:
- Description of the recon
- JS file URL
- Exact exposed key location
- The validation proof
- Potential attacker impact
- Recommended mitigations
Within a few days:
- The team fixed the issue
- Revoked the leaked key
- Regenerated a secure one
- Awarded a bounty 💰
The researcher called it a “₹₹₹₹₹ moment” - a well-deserved reward.
Defensive Perspective (Deep-Dive)
1. Why did this leak happen?
Most likely:
- The frontend build pipeline included environment variables directly
- Developers placed sensitive keys in a config.json
- No secret scanning tools were running in CI/CD
- The microservice depended on client-side speech processing
- CORS wasn’t restricted properly
2. How organizations should prevent cloud API leaks
A minimal defensive checklist:
a) Never expose backend keys in frontend JS
Use:
- Server-side proxies
- Role-based API keys
- Signed URLs
b) Use Azure Managed Identities
This eliminates the need for static keys.
c) Enforce key rotation policies
Keys must rotate every 30-90 days.
d) Enable Azure cost alerts
Alerts for:
- Unusual spikes
- Request volume anomalies
- Region anomalies
e) Implement CI/CD secret scanning
Tools:
- GitHub Secret Scanning
- Gitleaks
- TruffleHog
- Semgrep Rules
f) Limit allowed IP ranges
Lock down Azure Cognitive Services to:
- Backend server IPs
- VNETs
- Specific firewalls
Troubleshooting & Pitfalls
“Blank Page” Doesn’t Mean “Nothing Here”
Many beginners give up when a page renders nothing.
Always inspect:
- JS files
- Network panel requests
- HTML source
- Response codes
- CDN-hosted assets
“Credential Leaks Are Low Severity”
Sometimes triage teams classify leaked credentials as low severity if:
- They are outdated
- Not tied to production
- Unreachable resources
But persistence pays off.
The next credential might be the one that truly matters.
“JS Files Don’t Have Secrets”
They do.
More often than you think.
Final Thoughts
This bug is the perfect example of why persistent recon is the greatest skill in bug bounty.
The researcher:
- Did not give up after low-severity reports
- Kept scanning subdomains
- Inspected a blank page instead of ignoring it
- Dug deep into JavaScript
- Recognized the value of cloud keys
- Validated safely
- Reported responsibly
- Earned a solid bounty
Modern applications rely heavily on cloud services.
This means cloud keys are everywhere.
Finding them is often worth more than finding a classical XSS.










