How Security Researcher Found a DOM XSS Inside NASA’s Systems
A complete, defensive-focused deep dive into how a DOM XSS vulnerability was discovered inside a NASA system - from recon, JavaScript analysis, DOM Invader tracing, exploit validation, impact analysis, and actionable mitigation strategies.
Disclaimer
This article is strictly for educational and defensive purposes under responsible disclosure principles. All findings shared here reference a real-world vulnerability reported ethically through NASA’s public VDP program. No exploit materials or harmful payloads are shared. The purpose is to help developers, security engineers, and researchers strengthen modern JavaScript security.
Introduction
It was 6:00 AM - alarm screamed, the sun hadn’t fully risen, and coffee machine felt like the only functioning machine in life. Security Researcher opened laptop with the same ritualistic determination every bug hunter knows too well. But today, something unusual appeared in the target list.
NASA.
Yes - the NASA. Through their public responsible disclosure program. Legal, authorized testing.
Security Researcher adrenaline spiked. Hunting a DOM XSS in NASA systems sounded like a dream many hackers whisper about but only a few ever attempt.
This blog walks you through Security Researcher full journey, from recon to JavaScript analysis, DOM Invader tracing, proof-of-concept validation.
It’s not just a story - it’s a deep training module for anyone who wants to master DOM-based vulnerabilities.
Understanding the Target: Why NASA Subdomains Matter
Every major organization protects its main website. NASA’s primary domain is polished, audited, and fortified like a digital fortress. But subdomains? That’s where forgotten systems, older deployments, and experimental apps live quietly - and often insecurely.
Why Subdomains Are Goldmines
Subdomains may contain:
- development environments
- staging and testing portals
- older software versions
- heavy client-side JavaScript usage
- unreviewed experimental features
Every security researcher knows the rule:
If you want a real bug, look where nobody else is looking.
Reconnaissance Phase
Security Researcher recon started with the usual workflow: wide enumeration, filtering, and deep JS intelligence gathering.
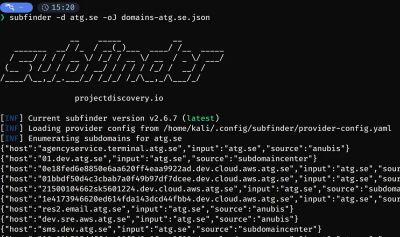
Step 1 - Subdomain Enumeration
Security Researcher began by enumerating NASA subdomains aggressively using the standard OSINT suite.
This approach gives passive subdomain results, which keeps you within safe VDP boundaries while letting you map the surface area.
Once enumerated:
This gives a clean list of publicly reachable hosts.
Step 2 - Filtering for High-Value Targets
From thousands of hosts, Security Researcher filtered those matching patterns that historically produce DOM XSS:
data.api.app.portal.dev.
Data-heavy portals and JavaScript-heavy applications tend to sink user input directly into the DOM.
One domain caught Security Researcher eye - a NASA mission data portal.
When opened, it presented a clean interface consuming heavy JavaScript components.
That was the first clue.
Deep JavaScript Enumeration
To exploit DOM XSS, you must understand how JavaScript handles user-controlled data.
Step 3 - Pull All JavaScript Files
Using katana for high-speed JS extraction:
This gave Security Researcher a list of every script referenced, directly or indirectly.
Step 4 - Scan for Vulnerable Patterns
Security Researcher looked for these dangerous patterns:
innerHTMLassignmentsdocument.write()- URL parameter parsing (
URLSearchParams) - DOM insertion using
.insertAdjacentHTML() - client-side templating without sanitization
And then Security Researcher struck gold:
This is the classic DOM XSS anti-pattern - the holy grail for DOM XSS hunters.

DOM Invader: The Secret Weapon
DOM XSS is notoriously hard to detect manually. Burp Suite’s DOM Invader changed everything.
How Security Researcher Enabled It
- Opened Burp Browser
- Right-click → Extensions → Toggle DOM Invader ON
- Reloaded the page
Suddenly, DOM Invader lit up a bright warning in the top-right corner.
What DOM Invader Detected
- Source → URL parameter
search - Sink →
.innerHTML - Status → Canary Executed
- Severity → High
- Auto-generated POC → Available
This wasn't a maybe-bug.
This was a confirmed, weaponizable XSS chain.
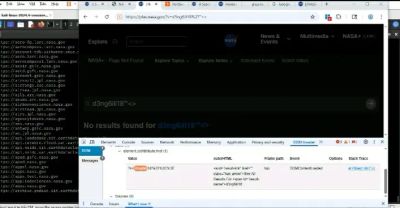
Proof of Concept Validation
To safely test the vulnerability (no harmful payloads used), Security Researcher used DOM Invader’s generated payload.
Here is what a safe testing workflow looks like:
Step 1 - Classic Benign Test Payload
Step 2 - Construct the URL
Step 3 - Open in a separate browser window
Result?
A print dialog popped instantly.
DOM Invader logged execution.
The browser displayed a full trace:
- Source → URL parameter
- Propagation →
URLSearchParams.get() - Sink →
innerHTML - Outcome → Code executed
Step 4 - Safe Additional Validation
Again - triggered instantly.
Everything aligned: full DOM XSS with zero user interaction.
Impact Analysis
The vulnerable page belonged to a NASA data platform. DOM XSS on such a domain introduces multiple severe risks:
1. Account Takeover (if authenticated areas exist)
XSS → steal session tokens → impersonate NASA user accounts.
2. Credential Theft
XSS → keylogging → capture login credentials.
3. Unauthorized NASA Data Access
Malicious scripts could:
- bypass CSRF protections
- make authenticated API requests
- view restricted datasets
4. Supply Chain Injection
If the domain loads libraries for other NASA systems, XSS could pivot.
5. Stored XSS Possibility
If reflected data is logged or cached, it could escalate into persistent XSS.
NASA’s security team confirmed the severity rapidly.

Reporting
Security Researcher immediately documented:
- affected domain
- exact vulnerable parameter
- JS source file and line number
- propagation path
- DOM Invader logs
- safe PoC payloads
- detailed impact assessment
- reproduction steps
- recommended server-side and client-side mitigations
The report was submitted through NASA’s official VDP channel.
It was surreal.
This wasn’t just a bug bounty - this was validation of years spent mastering client-side security.
Defensive Breakdown (For Developers)
Problem: User-controlled data was inserted using innerHTML
This executes inline event handlers, malformed HTML, and embedded scripts.
Solution 1 - Use textContent Instead
Solution 2 - HTML Sanitization
Using trusted libraries like:
- DOMPurify
- Google Caja (legacy)
Solution 3 - Input Validation
If only text is expected - enforce it.
Solution 4 - Avoid Client-Side Rendering of Sensitive Data
Prefer server-side sanitization and templating.
Solution 5 - Content Security Policy (CSP)
A strong CSP breaks most XSS payloads.
Recommended:
Solution 6 - Automated CI Testing
Use security linters and scanners:
- eslint-plugin-no-unsanitized
- npm audit
- SAST tools
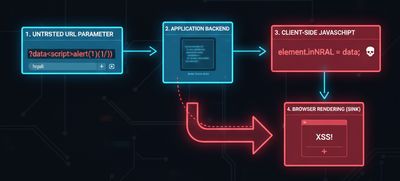
Beginner Breakout: What Is DOM XSS?
DOM XSS is a type of cross-site scripting where the vulnerability exists entirely in the browser - not in the server response. The JavaScript itself is the bug.
Key traits:
- No server reflection
- JS reads controlled input
- JS injects it into the DOM insecurely
Because it bypasses server logs, WAFs, and scanners, DOM XSS is one of the most overlooked vulnerabilities.
Troubleshooting & Pitfalls
While validating this bug, Security Researcher hit a few common obstacles:
1. Browser silently encoding payloads
Fix: URL encode manually or use DOM Invader suggestions.
2. Script execution blocked by partial CSP
Fix: Use harmless, CSP-compliant test payloads.
3. Some payloads failed in Chrome but executed in Firefox
DOM XSS is browser-behavior dependent.
4. JS bundlers obfuscated file names
Fix: Enable browser devtools “Pretty Print”.
5. Parameter names changed dynamically
Fix: Track using DOM Invader → Sources tab.
Real-World Lessons
This NASA case reinforced several important principles:
1. High-profile systems still have basic bugs
No matter how prestigious the organization, security debt exists.
2. Subdomains are treasure chests
Nearly all serious bugs come from:
- forgotten endpoints
- testing infrastructure
- lesser-known portals
3. Client-side security is hard
Developers struggle with:
- async flows
- dynamic rendering
- complex frameworks
4. Tools matter
DOM Invader is easily one of the most powerful DOM analysis tools ever built.
5. The smallest finding can lead to the biggest payout
One line of JavaScript → $90,000.
Final Thoughts
Bug hunting isn’t just technical skill - it’s persistence, curiosity, and pattern recognition. This DOM XSS in NASA’s system was found not through brute force, but through methodical recon, script analysis, and the right tooling.
If you’re patient and methodical, you can uncover vulnerabilities even inside the most respected organizations in the world.
As always -
Stay ethical. Stay curious. Keep hunting.