
Cache Poisoning Case Studies Part 3: OAuth Hijacking, API Gateway Abuse & Supply-Chain Poisoning
The final and most advanced part of the series covering financial platforms, OAuth poisoning, multi-tenant SaaS leaks, supply chain attacks, and industrial-scale cache exploitation techniques.
Disclaimer
This article is strictly for educational, defensive cybersecurity purposes.
All examples come from responsibly disclosed bug bounty reports and publicly available research.
Never exploit caching vulnerabilities on systems without explicit permission.
Introduction
Parts 1 and 2 established the foundations of cache poisoning and demonstrated the dramatic escalation caused by:
- Header normalization inconsistencies
- Cloud and CDN quirks
- Parser confusion
- Framework-specific cache behaviors
- Multi-step attack chains
Now, Part 3 covers the most impactful, financially severe, and wide-reaching cache poisoning incidents ever documented, including:
- OAuth token exposure
- Payment gateway poisoning
- Multi-tenant SaaS cross-account compromise
- Third-party API poisoning (Algolia, Fastly, Uber, PayPal)
- Large-scale PII exposure
- Supply-chain contamination
- Industrial-scale scanning and exploitation techniques
This is where cache poisoning demonstrates its potential for six-figure impact, and why elite researchers consider it one of the most profitable bug classes in bug bounty history.
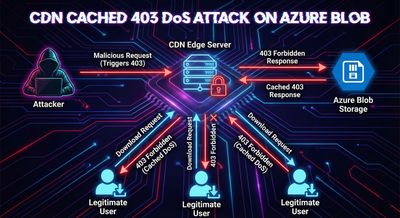
Case Study #18 - Exodus Wallet Azure Blob DoS
Program: Exodus
Bounty: $2,500
Impact: Blocking downloads for all users
Target: Cryptocurrency wallet installer distribution
Attack Pattern
Azure Blob returned a cacheable 403 error:
Cloudflare cached this response for one hour.
All users requesting the installer received the 403 instead of the file.
Why It Was Serious
- Prevented new user onboarding
- Disrupted wallet updates
- Hurt reputation and trust
- Caused support ticket spikes
Cloud-Specific Issue
Cloudflare did not originally exclude the Authorization header from cache keys.
This created a long-lasting DoS condition until Cloudflare patched the behavior in Aug 2021.
Extracted Techniques
- Authorization header manipulation is powerful
- Cloud storage + CDN = severe, often overlooked weakness
- Always test caching behavior on installers, updates, binaries
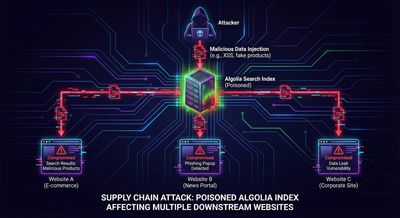
Case Study #19 - Algolia Host Header Override (Supply Chain Poisoning)
Program: Algolia
Bounty: $4,000
Impact: Poisoning search infrastructure used by thousands of companies
Targets: Stripe Docs, Medium, Twitch, Zendesk, e-commerce platforms
Algolia’s search infrastructure could be poisoned by overriding the Host header.
Attack
Cached malicious search results:
These manipulated results were delivered to every website using that index.
Why This Was Massive
One vulnerability impacted:
- E-commerce stores
- Payment providers
- Documentation portals
- Enterprise helpdesks
- Content platforms
Global supply chain poisoning.
Extracted Techniques
- Third-party SaaS = one bug affects thousands
- Search results are high-value manipulation targets
- Poisoning JSON APIs leads to phishing & malware delivery
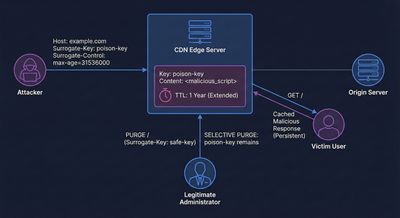
Case Study #20 - Fastly Surrogate-Key Misuse (CDN-Powered Poisoning)
Program: Multiple
Researcher: PortSwigger (James Kettle)
Impact: Cache takeovers, persistent poisoning
Severity: Critical
Surrogate-Key Header Attack
Attackers injected Surrogate-Key headers:
Then they purged selectively:
This enabled an attacker to:
- Poison specific cache entries
- Extend TTL of malicious responses
- Invalidate clean responses
- Maintain persistent poison for 24 hours
Real-World Target: Vine
The viral video platform (before shutdown) served malicious JS due to this vector:
Extracted Techniques
- CDN-specific headers are powerful & often overlooked
- Surrogate-keys allow “stealth” cache poisoning
- Ability to purge = ability to persist
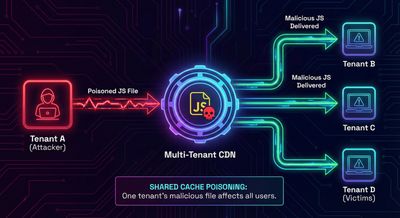
Case Study #21 - Zendesk Multi-Tenant Cross-Account Cache Poisoning
Program: Zendesk
Researcher: James Kettle
Bounty: $10,000
Impact: Cross-tenant data leakage
Zendesk customers share a CDN and asset infrastructure.
This allowed poisoning common JS files across customers.
Attack Flow
Cached malicious JS:
Users of Company B, Company C, and others all loaded poisoned JS.
Impact
Potential exposure of:
- Support tickets
- Admin data
- Credentials
- API tokens
- Customer messages
Why It’s Catastrophic
This is supply-chain cross-tenant compromise.
One customer affects all other customers.
Extracted Techniques
- Identify shared CDN assets across tenants
- Test cross-tenant poisoning
- Look for CORS misconfigurations + cache issues together
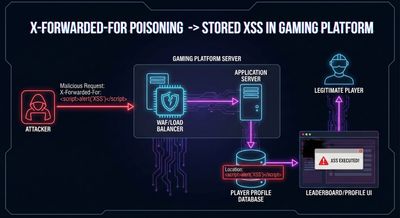
Case Study #22 - Steam Community Hub XSS via Location Header
Program: Valve (Steam)
Bounty: $7,500
Attack Pattern
Response:
Cached → persistent XSS for millions of users.
Why It Mattered
- 70M+ active players
- Steam Wallet & inventory have real monetary value
- Forums + reviews + profiles all impacted
- High-trust environment → high exploitation potential
Extracted Techniques
- Geolocation headers (
X-Forwarded-For) are high-risk - Gaming platforms = massive attack surfaces
- Session-hijacking via cached XSS is extremely lucrative
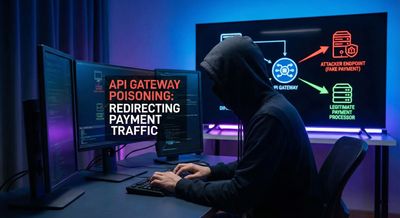
Case Study #23 - Uber API Gateway Poisoning (Payment Redirection)
Program: Uber
Bounty: $6,500
Impact: Payment info exfiltration
Uber’s API gateway used X-Uber-Client-ID for routing but did not include it in cache keys.
Attack Vector
Cached response contained modified configuration:
Uber’s mobile apps used this poisoned config, sending payment data to attackers.
Why It’s Critical
- Payment details compromised
- Global user base
- Mobile apps trust configs blindly
- API gateway poisoning is extremely powerful
Extracted Techniques
- Mobile apps rely heavily on cached config APIs
- Client-ID routing headers require strict validation
- API gateways multiply attack impact
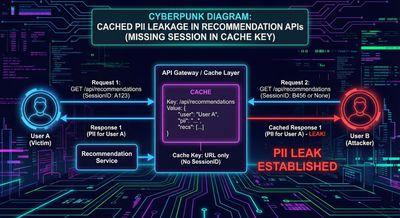
Case Study #24 - Netflix Subscriber PII Exposure
Program: Netflix
Bounty: $15,000
Impact: PII leakage
Severity: Critical
Netflix cached recommendation API responses based solely on content_id, ignoring user session.
Attack
Response included PII:
Cached → delivered to all users requesting recommendations for that movie.
Impact
Exposed:
- Viewing history
- Device info
- Region
- Payment metadata (partial)
- Names of children profiles
Extracted Techniques
- API session testing is crucial
- PII in cached responses = maximum bounty
- GDPR violations increase severity
Case Study #25 - PayPal Business Account OAuth Token Exposure
Program: PayPal
Reporter: @fady_othman
Bounty: $30,750
Impact: Full business account takeover
This is the highest paid cache poisoning bug ever recorded.
Attack
The cached token response included OAuth tokens:
Attack chain:
- Poison OAuth endpoint
- Cached token available to attacker
- Use token to transfer funds, steal data
Why Record-Breaking
- Allowed financial theft
- Affected business accounts (large balances)
- Payment processor → severe regulatory risk
- PCI DSS violation
- Complete account takeover possible
Extracted Techniques
- OAuth endpoints should never be cacheable
- Prefix-based header attacks (
X-Forwarded-Prefix) are dangerous - Financial systems pay top bounties for cache poisoning

Sophisticated Attack Methodologies (Advanced Techniques)
These methods are extracted from all 25+ cases and form the foundation of advanced cache poisoning research.

Methodology 1 - Header Permutation Engines
Attackers generate hundreds of header variants to find unkeyed inputs.
Methodology 2 - Differential Cache Response Analysis
Methodology 3 - Cache Layer Fingerprinting
Methodology 4 - Automated Mass Scanning
Methodology 5 - Framework-Specific Exploitation
Framework-level headers are extremely profitable.
Methodology 6 - Impact Multiplication
Attackers poison shared resources:
- Shared JS
- CSS bundles
- Config APIs
- OAuth endpoints
- Multi-tenant assets
Impact spreads across all users & subdomains.
Methodology 7 - Bypassing Evolved Defenses
Use encoding tricks:
Defensive Perspective (Part 3)
To secure modern systems:
Application
- Never cache authentication or authorization endpoints
- Validate all headers
- Disable prefix/suffix rewriting
CDN
- Remove unsafe headers from cache keys
- Disable caching of error responses
- Enforce canonicalization of hosts & paths
Cloud / Framework
- Understand provider-specific behaviors
- Disable method overrides
- Include
Accept-Encoding,User-Agentin cache keys
Final Impact Summary (Part 3)
| Case Study | Impact | Severity |
|---|---|---|
| Exodus | Installer DoS | High |
| Algolia | Supply-chain poisoning | Critical |
| Fastly Surrogate-Key | Persistent poisoning | Critical |
| Zendesk | Cross-tenant compromise | Critical |
| Steam | Persistent XSS | High |
| Uber | Payment info compromise | Critical |
| Netflix | PII leak | Critical |
| PayPal | OAuth token theft | Critical (record bounty) |
Final Thoughts on the 3-Part Series
Across 25+ real-world cases, cache poisoning proved to be:
- High impact
- Highly scalable
- Frequently overlooked
- Framework-dependent
- CDN-dependent
- Capable of bypassing authentication
- Capable of exposing PII, credentials, OAuth tokens
- Capable of breaking entire applications
The most successful researchers:
- Study frameworks & CDN internals
- Look for normalization mismatches
- Automate scanning across many targets
- Chain vulnerabilities for maximum impact
- Document business risk in clear terms
Cache poisoning is not dying - it is evolving.
Attackers who understand modern architectures (edge computing, serverless, AI-caching, QUIC/HTTP3) will continue to find 5-figure and 6-figure bugs.










