
CVE-2025-64446: Lessons From a FortiWeb RCE Chain That Shook Enterprise Perimeters
An educational deep dive into CVE-2025-64446, a critical FortiWeb vulnerability chain combining path traversal and authentication bypass, with defensive lessons for blue teams and architects.
Disclaimer
This article is written strictly for educational and defensive security purposes.
It analyzes a publicly disclosed vulnerability to help organizations understand root causes, impact, and prevention.Do not attempt to test or reproduce any behavior described here on systems you do not own or have explicit authorization to assess.
Introduction
Enterprise security appliances are designed to be the final line of defense. When they fail, they fail loudly.
In late 2025, the security community was forced to confront that reality again with CVE-2025-64446, a FortiWeb vulnerability chain that demonstrated how multiple “small” trust assumptions can collapse into unauthenticated, remote administrative control.
What made this vulnerability particularly dangerous was not a single bug, but a chain of architectural weaknesses:
- Improper URL parsing
- Unsafe path traversal handling
- Exposure of internal CGI handlers
- Blind trust in client-supplied identity headers
Individually, each issue might have been survivable. Together, they formed a straight path to full compromise.
This blog reframes the incident not as an exploit recipe, but as a case study in secure appliance design.
Why FortiWeb Vulnerabilities Have Outsized Impact
FortiWeb sits in a uniquely sensitive position:
- It terminates TLS
- It inspects and rewrites traffic
- It often has administrative access to upstream services
- It is trusted implicitly by internal teams
A vulnerability at this layer is not “just another web bug.”
It is a perimeter collapse.
That context is critical when evaluating CVE-2025-64446.
High-Level Overview of CVE-2025-64446

CVE-2025-64446 is best understood as a chained vulnerability, not a single flaw.
At a high level, the chain looked like this:
- API routing confusion via encoded characters
- Path traversal escaping the intended API sandbox
- Direct access to an internal CGI handler
- Authentication bypass through forged identity metadata
- Privilege escalation to full administrative control
All of this occurred pre-authentication.
Reconnaissance and Exposure Reality
The first uncomfortable truth: many FortiWeb management interfaces were internet-exposed.
From a defensive standpoint, this was the first failure.
Search engines and asset discovery platforms made exposure trivial to confirm:
Common indicators included:
- Management portals on 443 or 8443
- Distinctive HTTP headers
- TLS certificate metadata referencing Fortinet
- Predictable API paths returning structured errors
Once exposed, the remaining question was versioning.
Vulnerable Version Ranges (Publicly Documented)
Based on vendor advisories and coordinated disclosure, the affected branches included:
| Branch | Vulnerable Versions |
|---|---|
| 7.0.x | 7.0.0 – 7.0.11 |
| 7.2.x | 7.2.0 – 7.2.11 |
| 7.4.x | 7.4.0 – 7.4.9 |
| 7.6.x | 7.6.0 – 7.6.4 |
| 8.0.x | 8.0.0 – 8.0.1 |
Many appliances leaked partial version hints through:
- Error responses
- Redirect chains
- HTML comments
- TLS certificate fields
The Core Design Failure: Unsafe API Routing

The heart of CVE-2025-64446 lies in how FortiWeb parsed API paths.
A specially crafted request abused URL-encoded characters in combination with traversal sequences, allowing the request to escape the intended API routing logic and reach an internal CGI binary.
Conceptually, the request path looked like this:
Key issues:
%3f(encoded?) confused the router- Traversal segments were not normalized early
- Internal CGI endpoints were not strictly isolated
- Security boundaries were assumed, not enforced
This alone would have been serious. But the next step is what made it catastrophic.
Authentication Bypass via Trusted Internal Headers

The internal CGI handler expected an identity context normally supplied by the authenticated GUI.
That context was passed through a header containing base64-encoded JSON describing the user.
Critically:
- No signature
- No integrity check
- No origin validation
If the header existed, it was trusted.
A representative structure looked like:
From a defensive perspective, this is a textbook violation of zero-trust principles.
The system assumed:
“If this header exists, it must be internal.”
That assumption did not hold.
From Access to Impact: Why This Was So Dangerous
Once the CGI handler accepted the forged identity, the attacker was effectively operating as an administrator.
This enabled:
- Creation of new admin accounts
- Modification of security policies
- Full configuration access
- Long-term persistence
At this point, the vulnerability crossed from “remote code execution risk” into complete appliance compromise.
Understanding the Exploit Artifact (Defensive Analysis)
Publicly circulated proof-of-concept scripts demonstrated how attackers chained these behaviors into a single request flow.
From a defensive lens, what matters is not the syntax, but what it reveals:
- The appliance trusted headers over session state
- Privilege decisions occurred too late in the request lifecycle
- Internal tooling was reachable from external interfaces
Any exploit artifact leveraging this chain is simply a symptom of those design choices.
Root Cause Summary
Stepping back, the failure was not a single missing check.
It was architectural:
- Routing logic mixed parsing and authorization
- Internal components were exposed rather than isolated
- Identity was represented as data instead of cryptographically enforced state
- Trust boundaries were implicit, not explicit
This is how “defense in depth” quietly collapses.
Defensive Lessons for Security Teams
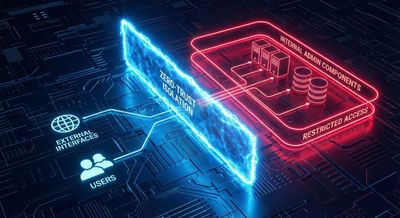
1. Isolate Internal Handlers Completely
Internal CGI tools should never be reachable through externally routable paths - even accidentally.
2. Normalize Before Routing
URL decoding, traversal normalization, and canonicalization must occur before access control decisions.
3. Never Trust Client-Supplied Identity
Headers are data, not authentication.
If identity is not cryptographically bound, it is attacker-controlled.
4. Reduce Appliance Attack Surface
Management interfaces should be:
- Network-restricted
- VPN-only
- Explicitly segmented
5. Design for Failure
Assume one control will fail - and ensure the next layer still holds.
Why This Case Matters Beyond FortiWeb
CVE-2025-64446 is not “just a Fortinet bug.”
It is a warning about:
- Trusting internal abstractions too much
- Assuming routing logic is a security boundary
- Letting convenience override isolation
These patterns appear again and again across security appliances, cloud control planes, and internal admin tooling.
Conclusion
CVE-2025-64446 will be remembered not for clever exploitation, but for what it revealed about implicit trust in security-critical systems.
The most important takeaway is simple:
If a system assumes trust instead of enforcing it, attackers will eventually prove that assumption wrong.
Security appliances must be built with the expectation that every boundary will be tested - because eventually, it will be.
References
- Fortinet Security Advisories
- MITRE CVE Database
- OWASP Top 10 – Broken Access Control
- NIST SP 800-53 – Trust Boundary Enforcement










