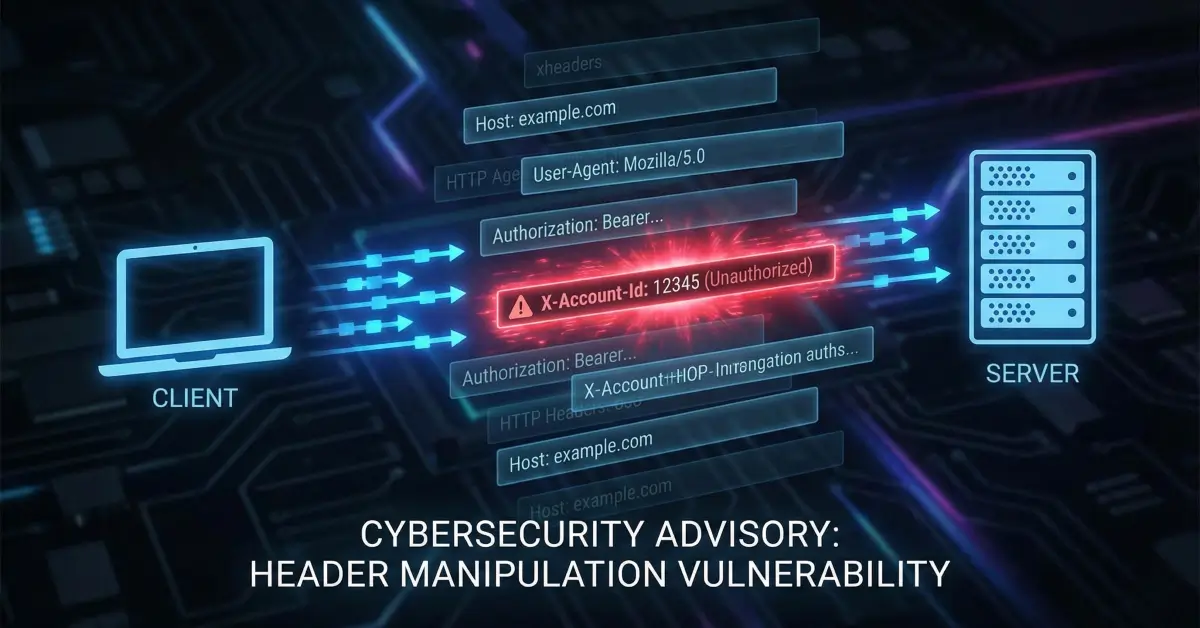
Critical Full Organization Takeover via Email Verification Bypass
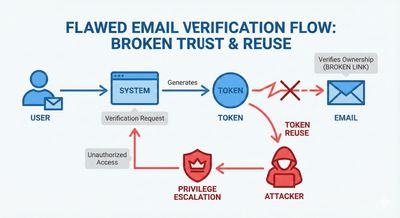
A critical business logic flaw where an email verification bypass enabled full organization takeover in a multi-tenant SaaS platform.
Disclaimer
This article is published strictly for educational and defensive security awareness.
All domains, identifiers, and sensitive values are redacted.
This write-up describes a vulnerability reported responsibly by another security researcher.
Introduction
This blog documents a critical business logic vulnerability discovered by a security researcher that resulted in a full organization takeover on a large multi-tenant SaaS platform.
The issue did not rely on memory corruption, race conditions, or advanced exploitation techniques. Instead, it stemmed from broken email verification logic, state desynchronization, and implicit trust in user-controlled parameters.
The result was catastrophic:
An unverified account could gain full administrative access to every organization associated with a corporate email domain.
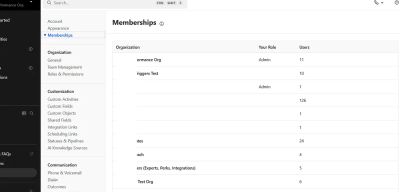
Platform Architecture Overview
The affected SaaS platform followed a common enterprise onboarding model:
- The first user registering with
@company.comautomatically creates the main organization. - Subsequent users registering with the same domain are auto-joined to that organization.
- Email verification is required to finalize account activation.
- Organization membership and role assignment are derived from the verified email domain.
This design is common — and safe only if verification tokens are correctly bound to identity state.
Vulnerability Summary
- Category: Business Logic Flaw
- Type: Email Verification Bypass
- Impact: Full Organization Takeover
- Severity: Critical
Step-by-Step Vulnerability Breakdown
Step 1: Initial Registration (Unverified State)
A user registers using a public email provider.
- Account is created successfully
- Email verification is pending
- A valid authenticated session cookie is issued
At this stage, the user is authenticated but unverified.
Step 2: Email Verification Link Structure
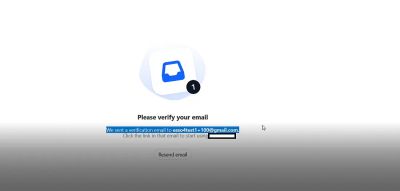
The platform sends an email verification link structured as:
Important observations:
- The email address is embedded directly in the URL
- The verification token is not cryptographically bound to the email
- The token remains valid even after identity changes
Step 3: Missing Verification Enforcement
While analyzing backend API calls, the researcher discovered that:
-
API authorization relied on:
- Session cookie
- CSRF token
- Organization ID header
-
No server-side enforcement existed to ensure
email_verified = true
This allowed unverified accounts to interact with sensitive identity endpoints.
Step 4: Email Change Before Verification
While still unverified, the user changed their email address to a corporate domain:
Result:
- Email updated successfully
- A new verification email is sent
- The original verification token remains valid
This created a state mismatch between account identity and verification tokens.
Step 5: Verification Token Reuse (Core Issue)
The original verification link was reused, with only the email portion modified:
Changed to:
The server:
- Accepted the request
- Marked the account as verified
- Trusted the modified email parameter
- Auto-joined the main organization
- Granted full administrative privileges
No token regeneration.
No email-token binding validation.
No secondary verification checks.
Root Cause Analysis
The vulnerability existed due to multiple compounded logic failures:
- Verification tokens not bound to email
- Email changes allowed before verification
- Verification tokens not invalidated after identity changes
- Trust in user-controlled URL parameters
- Automatic organization join based solely on email domain
Impact Assessment
Successful exploitation results in:
-
Full admin access to all organizations under
company.com -
Access to:
- Customer records
- Internal chats and files
- Billing data
- API keys and integrations
-
Complete compromise of tenant isolation
This represents a single-request, full-platform compromise.
Defensive Remediation Guidance
1. Bind Tokens to Identity State
-
Verification tokens must be bound to:
- Account ID
- Email address
- Issuance timestamp
2. Invalidate Tokens on Email Change
- Any email change must invalidate all existing verification tokens.
3. Enforce Verification Server-Side
- Critical endpoints must verify
email_verified = true. - Never rely on frontend-only checks.
4. Avoid Trusting URL Parameters
- Identity must be derived exclusively from server-side state.
5. Harden Auto-Join Logic
- Require explicit admin approval or domain ownership validation for enterprise joins.
Key Takeaways
- Email verification is a security boundary, not a UX feature
- Identity mutations must invalidate trust artifacts
- Business logic flaws can be more damaging than technical exploits
- Multi-tenant SaaS platforms must treat verification as authorization-critical
Final Thoughts
This vulnerability demonstrates how small logical assumptions can lead to massive security failures.
No exploit chains.
No brute force.
No zero-days.
Just a system that trusted user-controlled state more than it should have.
Security failures like this remind us that correct logic is as important as correct code.