The Header No One Was Watching: How a Single Client-Controlled Header Leaked Financial Data
A real-world business logic flaw where a trusted HTTP header silently caused sensitive financial data exposure. This case study explains how header-based IDOR happens, how to detect it, and how to prevent it.
Disclaimer
This article is published strictly for educational and defensive security purposes.
All targets, endpoints, identifiers, and data are redacted or generalized.
No testing was performed outside authorized environments, and no real user data was accessed.
Always test only on systems you own or have explicit permission to assess.
Introduction
Some vulnerabilities announce themselves loudly.
They crash applications, throw stack traces, or break features so visibly that anyone can see something is wrong.
Others are far more dangerous—because they blend in perfectly.
This write-up documents a header-based Insecure Direct Object Reference (IDOR) vulnerability discovered by a security researcher in a financial platform. Nothing looked broken. Nothing behaved unexpectedly. The application was polished, predictable, and stable.
That’s exactly why the bug survived.
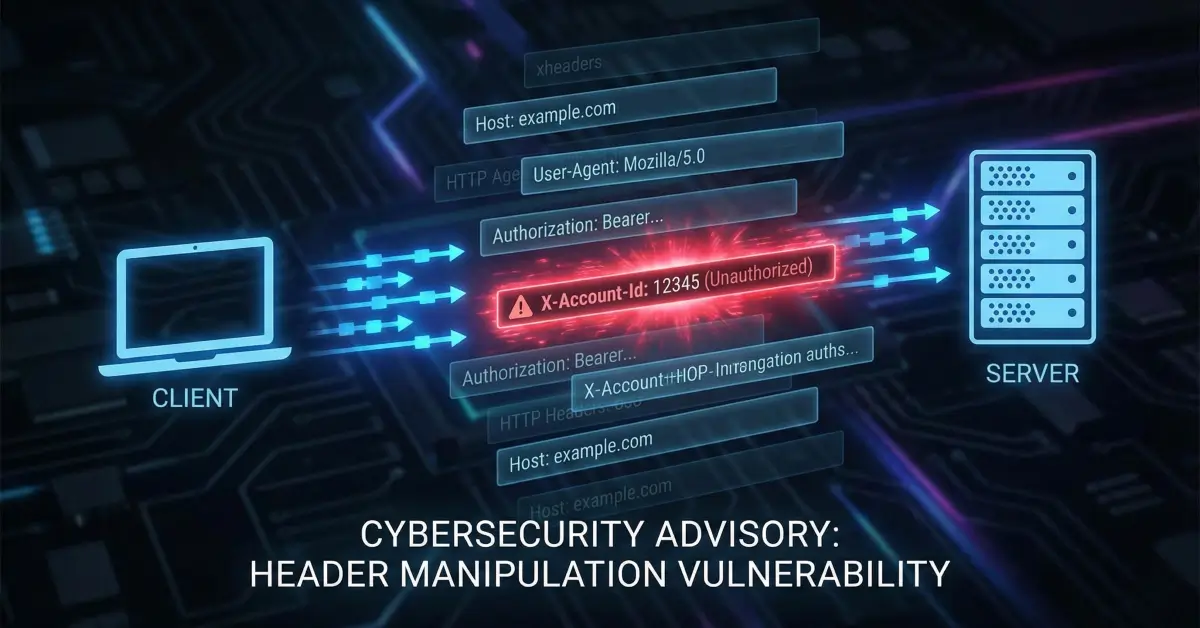
At the center of the issue was a single HTTP header—quietly trusted by the backend to decide which account’s data a user was allowed to see.
The Subtle Pattern That Raised Suspicion
When analyzing API traffic, experienced researchers often develop a sense for “normal” behavior:
- Authentication headers appear consistently
- JWTs or session cookies define identity
- Object IDs are derived server-side
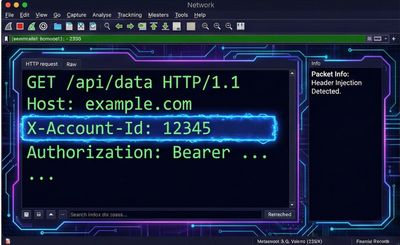
In this case, one request stood out for being too simple.
At first glance, it looked harmless.
Custom headers are common—used for routing, analytics, or internal convenience.
But this header wasn’t decorative.
It was authoritative.
Initial Validation: Baseline Behavior
The researcher replayed the request without any modification.
Result:
- The response returned the researcher’s own financial data
- Transaction history loaded normally
- No anomalies or errors
Everything behaved exactly as expected.
This established a clean baseline.
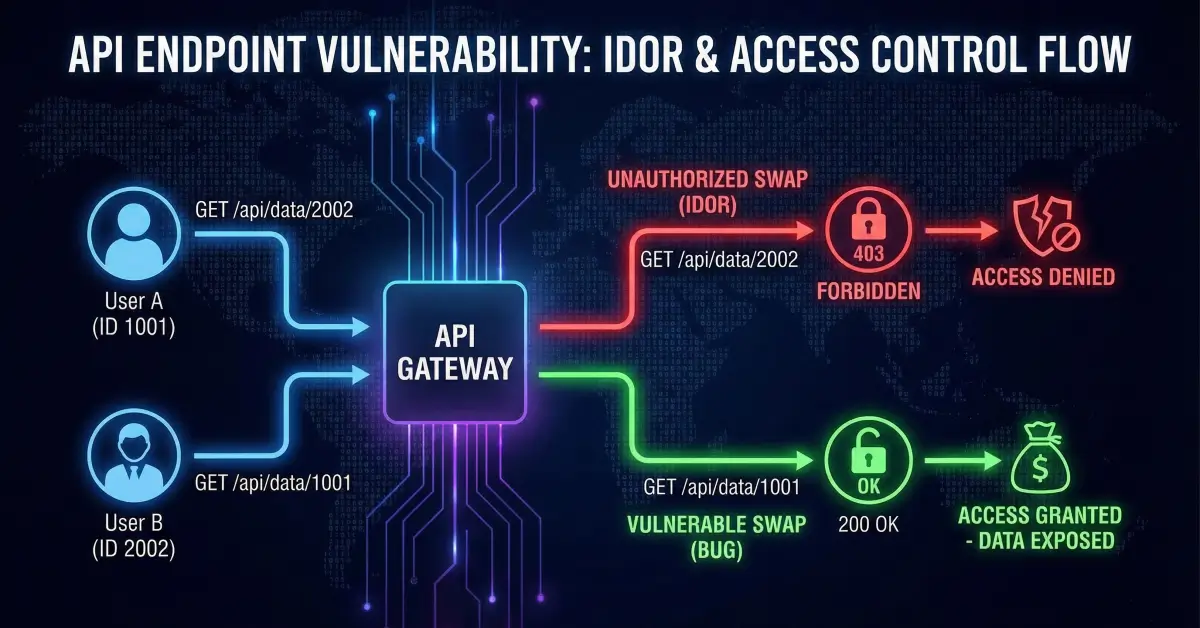
The Critical Test: Changing Only One Value
Next, the researcher made a minimal change:
- Same session
- Same authentication
- Same request body
- Same endpoint
Only one field changed.
The request was sent.
The response returned another account’s full financial data.
No warnings.
No access denied.
No ownership checks.
Just data.
What Actually Went Wrong
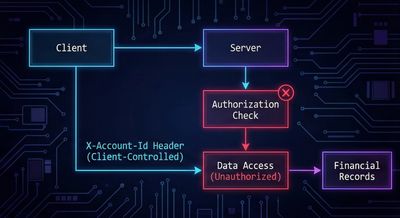
The vulnerability was not about missing authentication.
The user was authenticated.
The failure was deeper—and more dangerous.
Root Cause
-
The backend did not use the JWT or session to determine account ownership
-
Instead, it trusted a client-controlled header to decide which account to query
-
No server-side validation confirmed that:
- The account ID belonged to the authenticated user
- The requester was authorized to access that account
In other words:
The client was allowed to declare its own identity context.
This is a classic Broken Access Control scenario, implemented in an unusually quiet way.
Expanding the Scope
After confirming the initial endpoint, the researcher carefully checked other related APIs—only using their own accounts.
The same pattern appeared repeatedly.
Affected functionality included:
- Past transaction history
- Rewards and balances
- Billing preferences
- Account-linked metadata
Each endpoint relied on the same header:
Every request trusted it.
Why This Is Especially Dangerous in Financial Systems

In financial platforms, authorization mistakes have amplified impact.
A single IDOR can lead to:
- Exposure of transaction histories
- Leakage of billing details
- Regulatory violations (PCI, GDPR, financial privacy laws)
- Loss of user trust
- Legal and reputational damage
Unlike UI-based IDORs, header-based flaws are:
- Invisible to end users
- Easy to automate
- Difficult to detect without proxy-based testing
This makes them high-risk even when exploitation appears “simple”.
Ethical Testing Boundaries
The researcher followed strict ethical guidelines:
- Only tested with accounts they personally owned
- Did not enumerate or brute-force IDs
- Did not access third-party data
- Stopped testing once the vulnerability was clear
The issue was evident without crossing any ethical or legal lines.
Reporting and Triage
When the vulnerability was reported, initial discussions focused on severity.
As with many authorization flaws, questions arose:
- Is this limited?
- Is it theoretical?
- Does it affect sensitive data?
Once additional affected endpoints were confirmed, the risk became undeniable.
In financial contexts, unauthorized access to transaction data is inherently high impact.
The response from the security team was professional:
- Clear communication
- Fast validation
- Willingness to reassess severity
- Timely remediation
A bounty was awarded within 24 hours.
Why This Bug Lived So Long
This vulnerability wasn’t caused by complexity.
It was caused by convenience.
Likely scenario:
- A header was added to simplify backend routing
- Authorization logic was assumed to exist elsewhere
- No one revisited the trust assumptions
- The system worked perfectly—until someone questioned it
Security failures often emerge not from malicious intent, but from implicit trust.
How to Detect Header-Based IDOR (Researcher Perspective)
When testing APIs, always:
- Inspect custom headers
- Ask what each header controls
- Modify identifiers while keeping authentication constant
- Observe whether authorization is enforced server-side
Headers to watch closely:
- X-Account-Id
- X-User-Id
- X-Org-Id
- X-Tenant
- X-Customer
If changing one header changes the data scope—without denial—you’ve likely found a serious issue.
Defensive Perspective: How This Should Have Been Built
What Went Wrong
- Authorization logic trusted client input
- No ownership checks on object access
- Identity context was externalized to the client
Secure Design Principles
-
Never trust client-controlled identifiers
-
Derive account context from:
- JWT claims
- Session state
- Server-side mappings
-
Enforce authorization on every request
-
Treat headers as untrusted input—always
A secure pattern looks like:
Not:
Key Takeaways
- IDOR doesn’t always live in URLs
- Headers can be as dangerous as parameters
- Authentication ≠ Authorization
- Trust boundaries must be enforced server-side
- Quiet bugs often cause the loudest damage
Closing Thoughts
This vulnerability didn’t rely on clever payloads or obscure edge cases.
It relied on a single assumption:
“The client wouldn’t lie.”
All the researcher did was ask the question the backend never did:
“What if this account ID isn’t mine?”
That was enough.
One header.
One trust decision.
And unrestricted access to sensitive data.
Sometimes, systems don’t break because they’re complex.
They break because they’re too trusting.
References
- OWASP Top 10 – Broken Access Control
- OWASP API Security Top 10 – API1: Broken Object Level Authorization
- NIST SP 800-53 – Access Control
- PortSwigger Web Security Academy – IDOR