IDOR That Exposed User PII: When a Single Parameter Breaks Privacy
A real-world Insecure Direct Object Reference (IDOR) case study showing how a predictable ID parameter exposed sensitive user PII, why reproduction failed initially, and what this teaches about access control.
Disclaimer
This article is written strictly for educational and defensive security purposes.
All targets, domains, and identifiers are anonymized.
Only test systems you own or have explicit authorization to assess.
Introduction
Not every impactful vulnerability starts with a complex exploit chain or an exotic payload.
Sometimes, it’s just a number.
This write-up walks through a real-world Insecure Direct Object Reference (IDOR) vulnerability that exposed personally identifiable information (PII) for multiple users—simply by changing a single URL parameter.
What makes this case especially interesting is not just the vulnerability itself, but the reproduction challenge: the bug only manifested under specific environments, leading to initial confusion during triage.
This is a perfect example of why IDOR remains one of the most common—and most dangerous—classes of web vulnerabilities.
Understanding IDOR (Quick Refresher)
An Insecure Direct Object Reference (IDOR) occurs when:
- An application exposes a reference to an internal object (ID, filename, key)
- The server fails to verify that the requesting user is authorized to access that object
- The attacker can manipulate the reference to access data belonging to other users
In simple terms:
“If I can change a number and see someone else’s data, access control is broken.”

Recon: Focusing on User-Driven Assets
After spending hours on a primary target without results, the researcher switched context—a decision many hunters can relate to.
Instead of chasing obscure endpoints, the focus shifted to user-driven pages:
- Signup forms
- Login portals
- Registration workflows
- Any page that processes or displays PII
A simple Google dork was enough to surface promising entry points:
Within minutes, a subdomain appeared that allowed submission of personal details.
The Initial Submission Flow
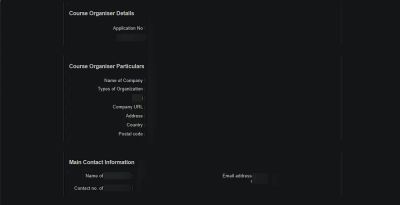
The application allowed a user to enter personal information and submit a form.
After submission, the browser was redirected to a public-facing success page:
At first glance, this looked normal—until the page rendered full personal details tied to the submission.
The Moment of Realization
Curiosity kicked in.
The researcher modified the URL parameter:
The page loaded.
And it wasn’t their data.
It was another user’s PII.
Incrementing the value again:
Yet another user’s sensitive information appeared.
At this point, the issue was clear:
- The
Idparameter directly mapped to backend records - No authentication check was performed
- No authorization validation existed
- The endpoint was publicly accessible
This was a textbook IDOR leading to unauthorized access to PII.
Why This Was High Impact
The exposed data included information users would reasonably expect to remain private, such as:
- Names
- Email addresses
- Contact details
- Organization-related information
From a security perspective, this violates:
- Privacy expectations
- Data protection regulations
- Basic access control principles
From a business perspective, it opens the door to:
- Mass data scraping
- Privacy complaints
- Regulatory scrutiny
- Reputation damage
Reporting… and the Unexpected Roadblock
The researcher documented the findings clearly and submitted the report.
However, triage responded with a familiar phrase:
“We are unable to reproduce the issue.”
At first, this seemed odd. The steps were straightforward.
But re-testing revealed something subtle—and important.
The Environment-Specific Twist
The vulnerability did not behave consistently across environments.
Key observations:
- On modern browsers → PII was visible
- On certain outdated browsers → page loaded, but no data appeared
- On some Unix-like environments → same result, no PII rendered
This explained why triage initially couldn’t reproduce the issue.
The vulnerability existed, but frontend rendering depended on environment-specific behavior.
Possible contributing factors included:
- Conditional JavaScript execution
- Browser-specific parsing
- Legacy compatibility code paths
- Client-side rendering differences
Why This Matters for Bug Hunters
This case highlights several critical lessons:
1. IDOR Can Be Contextual
A vulnerability may exist but only manifest under specific:
- Browsers
- OS environments
- User agents
- Rendering paths
Always test across variations when reproduction fails.
2. Reproduction Issues ≠ Invalid Bugs
If triage can’t reproduce immediately, it doesn’t mean the bug is invalid.
It often means more context is needed.
Clear communication wins here.
3. PII Exposure Escalates Severity
Even a “simple” IDOR becomes high-impact when:
- The data is sensitive
- The endpoint is unauthenticated
- Enumeration is trivial
Root Cause Analysis
At its core, the vulnerability existed because:
- The
Idparameter was treated as a trusted identifier - The backend fetched records directly based on that ID
- No ownership or session validation was performed
- The endpoint was publicly accessible
In short:
The server trusted user-controlled input as authority.
How This Should Have Been Designed
A secure design would enforce:
- Authentication: only logged-in users can access the page
- Authorization: users can only access records they own
- Indirect references: use random, non-guessable identifiers
- Server-side enforcement: never rely on client-side hiding

Defensive Recommendations
1. Enforce Object-Level Authorization
Every request must verify:
- Who is making the request
- Whether they own the requested object
2. Avoid Predictable Identifiers
Sequential numeric IDs are enumeration-friendly.
Prefer:
- UUIDs
- Indirect references
- Per-user scoped identifiers
3. Do Not Expose Sensitive Data on Public Endpoints
Success pages should not render PII without strict checks.
4. Test Across Environments
Security testing should include:
- Multiple browsers
- Different OSes
- Mobile vs desktop rendering
Lessons for Security Teams
- Don’t dismiss reports due to initial reproduction issues
- Ask for environment details early
- Understand that frontend behavior can hide backend flaws
- Treat PII exposure with urgency
Final Thoughts
This vulnerability didn’t require:
- Exploit chains
- Advanced payloads
- Race conditions
It required only one thing:
Trusting a number.
IDOR vulnerabilities remain one of the most common causes of large-scale data exposure—not because they’re complex, but because they’re easy to overlook.
This case is a reminder that access control must be enforced everywhere, every time, without assumptions.
References
- OWASP Top 10 – Broken Access Control
- OWASP IDOR Prevention Cheat Sheet
- Real-world bug bounty IDOR disclosures
- Privacy-by-design principles