How a Security Researcher Received an Appreciation Letter from NASA for Identifying a CVE
A real-world bug hunting case study explaining how a reflected XSS vulnerability (CVE-2025-0133) in PAN-OS GlobalProtect was identified on a NASA system and responsibly disclosed, resulting in an official appreciation letter.
Disclaimer
This article is published strictly for educational and defensive security awareness purposes.
All sensitive assets, domains, and identifiers are redacted.
No exploitation beyond safe proof-of-concept testing was performed, and all findings were disclosed through an authorized vulnerability disclosure program.
Never test systems without explicit permission.
Introduction
Bug hunting is rarely predictable.
Sometimes vulnerabilities surface within minutes. Other times, days of effort lead nowhere. And occasionally, a single late-night attempt uncovers a vulnerability on a high-profile system—turning persistence into recognition.
This write-up documents how a security researcher identified a real-world vulnerability, CVE-2025–0133, affecting a critical VPN component used by a NASA-operated system, and how responsible disclosure ultimately resulted in an official Appreciation Letter from NASA.
This is not a story of luck or automation—it is a case study in knowledge reuse, persistence, and contextual understanding of vulnerabilities.
About CVE-2025–0133
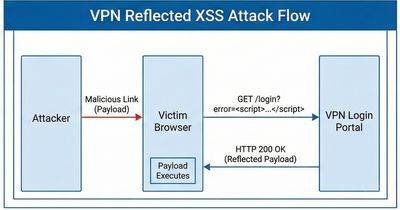
Vulnerability Type: Reflected Cross-Site Scripting (XSS)
Affected Product: Palo Alto Networks PAN-OS GlobalProtect
Severity: Medium
What the Vulnerability Allows
CVE-2025–0133 exists due to improper sanitization of user-controlled input in a GlobalProtect endpoint. An attacker can craft a malicious URL that, when accessed by an authenticated user, results in JavaScript execution in the browser.
Potential impact includes:
- Credential theft via phishing
- Session compromise in clientless VPN portals
- Abuse of trust in authentication infrastructure
- Targeted social engineering attacks
Although classified as reflected XSS, the deployment context—enterprise VPN and captive portals—significantly increases its real-world risk.
The Late-Night Context
After repeated unsuccessful attempts on the same program—mostly duplicates and informational reports—the researcher revisited a known CVE they had previously studied in depth.
Rather than searching blindly, the approach shifted to leveraging existing vulnerability knowledge and applying it to fresh targets.
This change in strategy became the turning point.
Reconnaissance Using Shodan
The researcher began with broad reconnaissance using Shodan to identify exposed PAN-OS systems.
Base Query
This returned a large number of publicly accessible PAN-OS instances.
Narrowing Scope to NASA
This refined query produced 11 results—a manageable scope for targeted validation.
Several hosts were tested without success. Near the end of the list, one host exposed a familiar GlobalProtect login interface.
Identifying the Vulnerable Endpoint
The following GlobalProtect endpoint is known to be affected in vulnerable PAN-OS versions:
This endpoint processes multiple user-supplied parameters, making it a common target for reflected XSS testing.
Payload Construction
The researcher crafted a payload injecting a harmless JavaScript prompt via an SVG-based XSS vector:
Proof of Concept Execution
When tested against the identified host, the payload resulted in JavaScript execution via a browser prompt—confirming the reflected XSS condition.
This demonstrated:
- User input was reflected without proper encoding
- The vulnerability was exploitable in a live environment
- The system was running an affected PAN-OS version
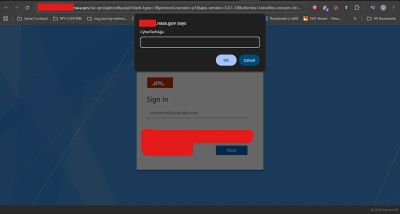
Validation on the Canonical Domain
To ensure accuracy and avoid false positives, the researcher repeated the test on the canonical NASA VPN domain (redacted).
The same payload produced the same result—confirming the vulnerability was not IP-specific but affected the actual production hostname.
Responsible Disclosure
The vulnerability was immediately reported through the official Bugcrowd Vulnerability Disclosure Program, including:
- Clear reproduction steps
- Impact explanation
- Sanitized proof-of-concept
- Reference to CVE-2025–0133
No sensitive data was accessed, modified, or exfiltrated during testing.
Outcome: NASA Appreciation Letter
Following triage and validation, the organization acknowledged the finding.
The final response included an official Appreciation Letter from NASA, recognizing the researcher’s contribution to improving security posture.
While no monetary reward was issued, the recognition itself became a career milestone—highlighting the value of responsible disclosure even in non-bounty programs.
Key Takeaways for Security Researchers
- Reusing known CVEs intelligently is powerful
- Context determines real-world impact
- Persistence often outperforms automation
- Final targets are sometimes the most rewarding
- High-profile organizations still benefit from external research
Lessons for Organizations
- VPN and authentication endpoints deserve continuous testing
- Reflected XSS in sensitive workflows should not be downgraded
- Patch validation must include external exposure checks
- Defense-in-depth matters even for “medium” CVEs
References
- Palo Alto Networks PAN-OS Security Advisories
- CVE-2025–0133
- OWASP Cross-Site Scripting Prevention Cheat Sheet
- Bugcrowd Vulnerability Disclosure Program Documentation