How to Get Your First CVE as a Beginner: A Practical, Real-World Guide
A beginner-friendly, real-world guide explaining how new security researchers can earn their first CVE by focusing on open-source projects, simple vulnerabilities, and responsible disclosure.
⚠️ Disclaimer
This article is written strictly for educational purposes. All activities described here should only be performed on systems you own, open-source projects, or targets where you have explicit authorization. Always follow responsible disclosure practices and applicable laws.
Introduction
For many people entering cybersecurity, the journey begins with bug bounties. You find a reflected XSS here, an IDOR there, maybe earn a small payout-or maybe receive a familiar “duplicate, thanks.”
At some point, a different goal appears:
“I don’t just want bounties. I want a CVE. I want my name in MITRE.”
That goal is not unrealistic. In fact, for beginners, getting a CVE is often more achievable than consistently earning bug bounty payouts-if you approach it the right way.
This guide is based on a real researcher’s experience and reframed into a structured, practical walkthrough. It avoids theory-heavy explanations and focuses instead on how beginners actually succeed in getting their first CVE.
What a CVE Really Is (And Why It Matters)
A CVE (Common Vulnerabilities and Exposures) identifier is a globally recognized ID assigned to a publicly disclosed security vulnerability.
A CVE exists to ensure that:
- A vulnerability is uniquely tracked worldwide
- Vendors and users can coordinate fixes
- Security tools (NVD, scanners, advisories) can reference it
- Researchers receive permanent public credit
Unlike bug bounty reports, which often remain private, a CVE is public, permanent, and historical. Your name becomes associated with the vulnerability across:
- MITRE
- NVD
- GitHub advisories
- Vendor changelogs
- Security research blogs
Bug bounties may pay money.
CVE credits build long-term reputation.
Bug Bounty vs CVE: A Reality Check
Bug bounty hunting and CVE research overlap technically-but they differ in outcome and mindset.
Bug bounty
- Target: a specific company
- Scope: limited to their assets
- Outcome: private fix, possible reward
- Visibility: usually none
CVE
- Target: software or libraries used by many
- Scope: global impact
- Outcome: public disclosure and recognition
- Visibility: permanent
Bug bounty rewards effort sometimes.
CVE credits effort forever.
For beginners especially, CVEs offer a clearer, more achievable path to recognition.
Where Beginners Should Actually Hunt
One of the biggest mistakes new researchers make is aiming too high, too fast.
You don’t need:
- Kernel exploits
- Router firmware bugs
- Enterprise appliances
Instead, start where success is realistic.
Beginner-friendly CVE targets
- Small open-source GitHub repositories
- Projects with 100–1000 stars
- WordPress plugins
- Node.js / Express applications
- Python Flask or Django projects
- PHP-based tools
- npm or pip packages
- Open-source Android apps
These projects often:
- Lack full security audits
- Have simple logic flaws
- Are maintained by approachable developers
- Welcome security help
Small project ≠ small impact.

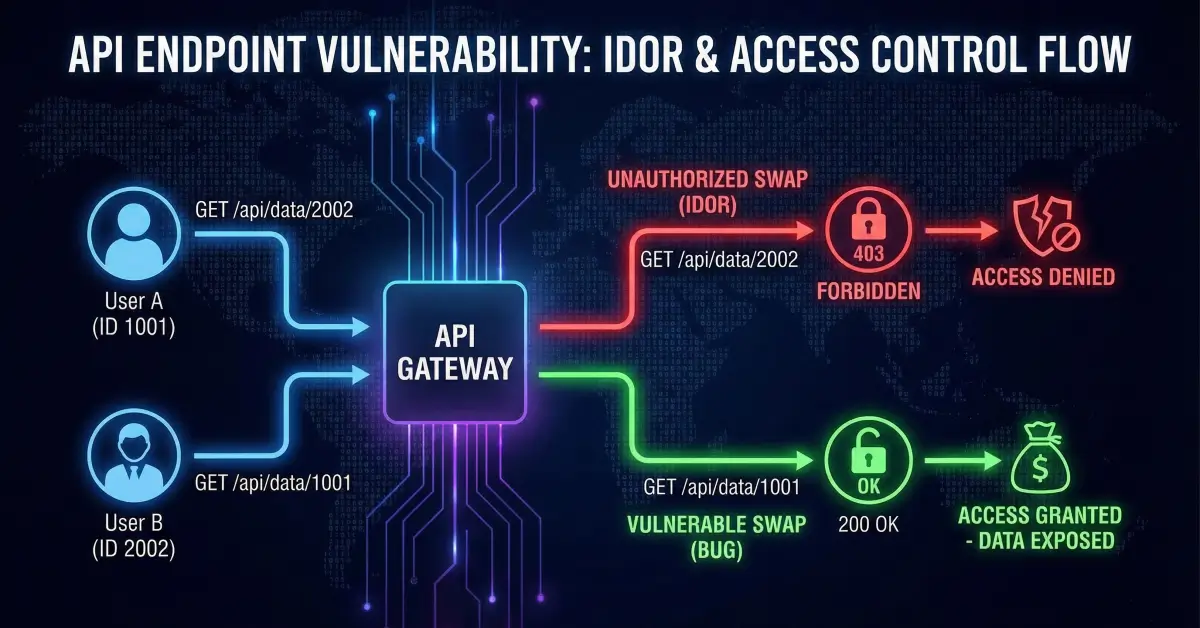
What Vulnerabilities Commonly Become CVEs
A common myth is that CVEs require extreme exploitation.
In reality, many CVEs are assigned for simple but impactful issues, such as:
- Missing authentication
- Default credentials
- IDOR in open-source APIs
- Information disclosure
- Broken password reset logic
- Hardcoded secrets
- Insecure file upload
- Directory traversal
- SSRF
- Unsafe configuration defaults
If you already hunt bug bounties, you likely know how to find these.
The difference is where you apply the skill.
Your CVE Hunting Toolkit
You do not need exotic tools.
A simple setup is enough:
- Burp Suite or an intercepting proxy
- Postman or curl
- VS Code
- GitHub search
- A local test environment
- Curiosity and patience
If you can test a bug bounty target, you can test an open-source project.
The Step-by-Step CVE Roadmap
This is where beginners usually fail-not because it’s hard, but because no one explains it clearly.
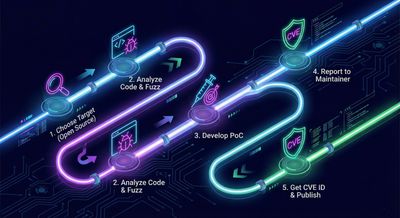
Step 1: Pick a realistic project
Avoid massive, heavily audited codebases.
Choose something small, functional, and actively used.
Examples:
- “Simple CRM”
- “Open-Source Inventory Tool”
- “File Upload Service”
- “Authentication Boilerplate”
Logic bugs thrive here.
Step 2: Run it locally
This is where CVE hunting becomes powerful.
Locally, you have:
- No rate limits
- No WAF
- Full code access
- Full endpoint visibility
You can test freely, safely, and deeply.
Step 3: Test like a bug bounty target
Once running, attack it exactly as you would a real application:
- Test authentication boundaries
- Check role separation
- Inspect APIs
- Try IDOR scenarios
- Abuse password resets
- Look for direct file access
- Explore hidden routes
- Inspect configs and backups
Many first-time CVEs come from moments like:
“Wait… this endpoint has no auth at all.”
That’s not luck. That’s observation.
Step 4: Document professionally
Good documentation matters more than fancy exploitation.
Your report should clearly include:
- Affected component and version
- Steps to reproduce
- Impact explanation
- Sanitized evidence
- Suggested remediation
Professionalism builds trust.
Step 5: Contact the developer respectfully
A simple message works:
“Hi, I’ve been using your project and discovered a security issue.
Would you like me to share details privately? I can also assist with a CVE if you’re open to it.”
Most maintainers appreciate this approach.
Step 6: CVE assignment
Two paths exist:
- The maintainer assigns a CVE (if they are a CNA)
- You request one directly from MITRE
MITRE’s process is formal, not hostile.
Clear details + cooperation usually lead to success.
What Happens After Your First CVE
A CVE changes how people perceive you.
Suddenly, you are:
- A published researcher
- Searchable in MITRE and NVD
- Referenced by scanners and advisories
- Taken seriously by recruiters
It is not about ego-it’s about credibility.

Common Beginner Fears (And Why They’re Wrong)
“My bug isn’t big enough”
Many CVEs are simple issues with broad impact.
“I’m not experienced enough”
Experience comes from doing-not waiting.
“Developers won’t take me seriously”
Professional communication changes everything.
Final Thoughts
Getting a CVE is not reserved for elite hackers.
It is reserved for curious, consistent, and respectful researchers.
If you can find bugs in bug bounty programs, you can find vulnerabilities in open-source software-often faster, with more impact, and with permanent recognition.
Your first CVE is closer than you think.
Go hunt.
Go break things legally.
Go leave your mark on the internet.