OAuth Authentication Bypass Leading to Massive PII Exposure: A Deep Technical Analysis
A detailed breakdown of how a misconfigured OAuth client_credentials flow exposed sensitive customer data at scale.
Disclaimer (Educational Use Only)
This article is published for ethical, educational, and defensive security purposes.
It does not reveal the identity of the affected organization, and no sensitive data is shared.
Readers must follow proper authorization rules and responsible disclosure practices at all times.
Introduction
There are security incidents that reveal themselves loudly, through obvious misconfigurations or predictable flaws. And then there are incidents that stay hidden behind layers of trust - the kind of issues that appear only when someone questions the assumptions baked into familiar systems.
This case belongs to the latter category.
The vulnerability originated from a small piece of the authentication pipeline on a commercial platform. At first glance, it followed the modern OAuth2 structure that countless applications rely on: authorization flows, tokens, validity checks, and granular scopes. Everything looked normal to the untrained eye.
But what began as routine reconnaissance - the kind performed by security researchers daily - slowly unraveled a critical oversight. The type of oversight that silently breaks the foundation of an entire security model.
By the time the researcher reached the core of the issue, one thing became clear: an OAuth misconfiguration had created a path that bypassed user identity completely, granting unauthorized access to sensitive personal data belonging to thousands of users.
This deep-dive breaks down what happened, how the issue was uncovered, and the security lessons that matter for every engineering and security team.
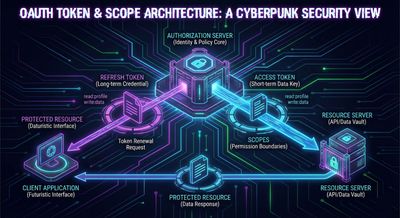
Understanding OAuth2 Through the Lens of This Incident
To understand how this vulnerability emerged, it helps to revisit how OAuth2 is supposed to work. Not from a theoretical standpoint, but from a practical, application-level perspective - the way real systems implement and rely on it.
OAuth2 is centered around delegation of access. Instead of credentials being passed around, tokens act as time-bound representations of permission. These tokens allow clients - apps, services, or interfaces - to access protected resources without exposing sensitive authentication details.
A typical OAuth deployment includes four major actors:
- User: the individual interacting with the system.
- Client: the application the user is using.
- Authorization Server: the entity responsible for validating identity and issuing tokens.
- Resource Server: the API or backend that actually hosts the protected data.
These four parties communicate through established “flows.” One of the most common is the Authorization Code Flow, where a user initiates access and explicitly grants permission.
This is the secure, human-in-the-loop approach most modern web applications rely on. It ensures that every token in circulation can be traced to a user and a consent decision.
But OAuth has other flows. And one of them - client_credentials - is where this entire story begins.

Understanding the client_credentials Flow (And Why It’s Dangerous When Misused)
The client_credentials grant type is often misunderstood. It was never designed for user login. Instead, it was built for system-to-system communication - backend services, daemons, or automated tasks. In this flow:
- There is no user.
- There is no login page.
- There is no consent.
- There are only machines.
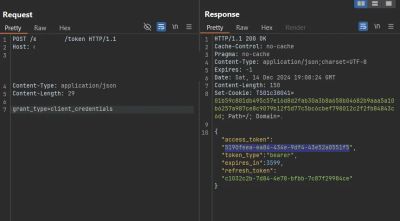
The client simply sends:
If the client_id and client_secret are valid, the server responds with an access token. This token represents the client itself, not any human identity. When implemented correctly, it is powerful and convenient. When implemented incorrectly, it becomes a direct bypass of user-based authorization.
That is exactly what unfolded in this case.

Reconnaissance: The Quiet Beginning of a Critical Discovery
The researcher was working within a wildcard scope, a common setup in private bug bounty programs. This meant that any subdomain under the organization’s main domain could be in scope, resulting in a broad attack surface.
The initial reconnaissance involved standard techniques:
- Subdomain enumeration
- Directory and file fuzzing
- Crawling archived pages
- Deep search engine queries
- Manual inspection of JavaScript bundles
Weeks of familiarity with the target had built a mental map: patterns in naming conventions, common backend structures, endpoint layouts, and authentication behavior. Nothing significant had emerged yet, but recon rarely pays off immediately - it pays off consistently.
The breakthrough came from an unexpected source: DuckDuckGo search results. A subdomain appeared that was not listed prominently elsewhere. It hosted a login page reachable at a path that most users wouldn’t know existed.
The login endpoint revealed behavior consistent with OAuth’s password grant type - another legacy flow that many platforms still use for mobile or internal applications. It accepted parameters like:
This alone wasn’t a vulnerability. But it provided a clue: the system was using an OAuth token endpoint. And token endpoints often expose behaviors developers don’t fully consider.
The Unexpected Breakthrough: Mutating the Grant Type
Token endpoints are often designed with strict validation. They should verify:
- Whether the grant_type is allowed
- Whether required parameters exist
- Whether the client credentials are present
- Whether the scopes match the policy
A small mutation can reveal large cracks. And that is what happened.
Instead of sending:
grant_type=password
The researcher crafted a request with:
grant_type=client_credentials
No other fields. No client_id. No client_secret.
The expectation? A clean rejection, or at least an authorization error.
What the system returned instead was astonishing:
A valid access token.
A valid refresh token.
No questions asked.
The token endpoint had made a fundamental assumption - that if the request came from a trusted application, it could relax checks. Unfortunately, this trust model was flawed.
This was no longer a login bug. It was an authentication bypass at the protocol layer.
Mapping the Hidden API Surface
Possessing a token is only useful if it grants access to something. The next step was to discover what the backend was protecting.
The platform’s frontend JavaScript bundles were inspected carefully. Internal applications frequently embed references to backend endpoints - even the ones they no longer use. These trails are valuable.
Only six relevant backend endpoints emerged through statically analyzing the scripts and observing network calls. The researcher attempted to call each one with the newly obtained access token.
Five of them rejected access.
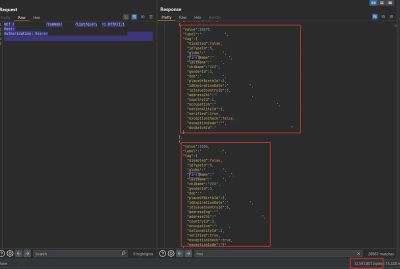
But the sixth endpoint didn’t just accept the token - it returned a large, structured JSON dataset.
And this dataset contained sensitive personal information: customer attributes, demographic details, identity fields, nationality codes, gender, basic profile data, and other fields that should never be accessible without strong authorization.
The initial response size: nearly 12MB of processed data.
A staggering amount for a single unauthenticated token.
Reconstructing the API Query Behavior
The accessible endpoint followed a simple pattern:
The value of query acted as a trigger for different slices of data. By adjusting the parameter, the researcher could retrieve additional sections of PII - all without authentication checks tied to a user identity.
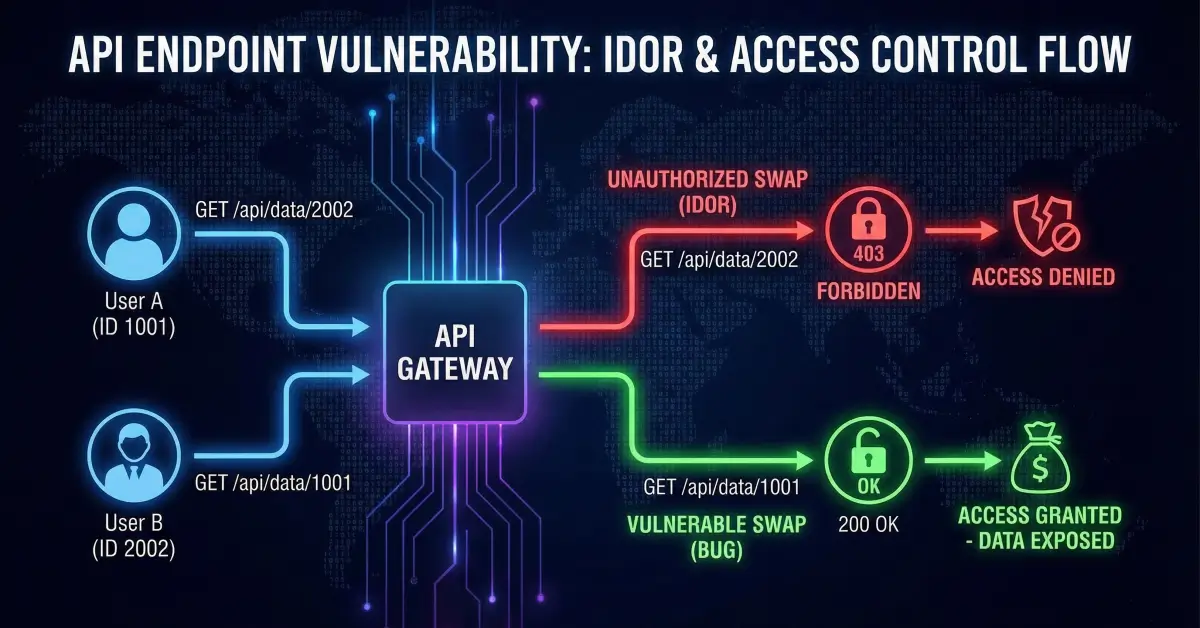
This is the core danger of misconfigured OAuth: a token that represents no user was being treated as a token that could access data meant only for authenticated individuals.
In practical terms, the API could be enumerated through harmless-looking query parameters, returning blocks of sensitive information at scale.
The issue was clear:
Authorization was designed around user scopes, but the token bypassed user existence entirely.
How the Vulnerability Was Reported and Triaged
Once the pattern was confirmed, the researcher prepared a responsible disclosure report. It contained:
- The exact HTTP request that triggered the token issue
- The endpoint that accepted the token without user identity
- A detailed explanation of why client_credentials must not grant access to user data
- A recommended remediation plan
- Proof-of-concept steps allowing the team to replicate the issue safely
The platform responded quickly. Given the severity and the potential impact on thousands of customers, the issue was escalated internally and addressed on the same day.
A fix was implemented by:
- Enforcing client_id and client_secret validation
- Blocking client_credentials for endpoints returning user-linked data
- Reintroducing proper scope checks for token issuance
- Reviewing API policies to ensure no other endpoints trusted machine tokens inappropriately
This type of rapid response is a sign of a security-mature organization.
Why This Bypass Worked: A Root-Cause Analysis
The vulnerability emerged from a combination of design oversights:
1. Missing Credential Validation
The token endpoint accepted client_credentials without verifying the sender’s identity. This effectively turned an M2M flow into a public entry point.
2. Incorrect Scope Binding
The access token carried permissions beyond what machine tokens should have. It accessed sensitive user-related resources that should have been limited to user-based flows.
3. Overly Broad API Permissions
The resource server treated all bearer tokens equally. No distinction was made between:
- Tokens representing users
- Tokens representing backend clients
- Tokens representing unprivileged components
4. Lack of Defense-in-Depth
Even if OAuth logic failed, secondary checks should have prevented bulk access to personal data.
Real-World Impact: What Could an Attacker Do?
The consequences of such a flaw are serious:
Extract Sensitive PII at Scale
Customer profiles, identity attributes, and other regulated data.
Bypass Authentication Entirely
No need for credentials, session tokens, or user involvement.
Enumerate Internal Behavior
By adjusting query parameters, attackers could map the data model.
Trigger Indirect Attacks
Even if the data is not financial, identity-related attributes can facilitate:
- Social engineering
- Account takeover targeting
- Phishing personalization
- Insider fraud
This is the type of bug that can quietly compromise trust.
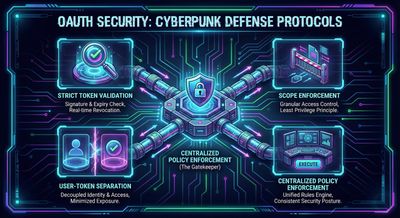
Defensive Perspective: Hardening OAuth Implementations
For organizations implementing OAuth2, several defensive principles must guide system design.
1. Treat Token Issuance as a Critical Security Boundary
The token endpoint is the gateway to everything else. Validation must be strict:
- Validate client_id
- Validate client_secret
- Validate allowed grant types
- Validate redirect URIs
- Validate scopes
2. Machine Tokens Must Never Access User Data
client_credentials should only access system metadata or backend workloads.
3. Enforce Fine-Grained Scopes
Tokens should not have broad permissions unless absolutely necessary.
4. Introduce Strong API Gatekeeping
Resource servers should inspect:
- Token type
- Token origin
- Intended audience
- Attached scopes
5. Test Authentication Flows Regularly
Penetration tests should include alternative grant types and malformed token requests.
6. Use Centralized Policies
Decentralized permission models increase the chance of misconfiguration.
Troubleshooting & Pitfalls (From a Defensive Lens)
Organizations often make assumptions about OAuth that lead them into subtle security gaps. Some common traps include:
- Assuming client_credentials is “safe” because it’s not user-based
- Allowing backend systems broad access without validating purpose
- Forgetting that bearer tokens do not confirm identity - only possession
- Relying solely on documentation instead of enforcement
- Treating machine flows as less risky than user-facing flows
These assumptions create precisely the kind of exploit surface described here.

Final Thoughts
This incident is a reminder of a simple truth in security engineering: complex systems do not always fail loudly. Sometimes they fail quietly, through a single missing check or a misconfigured flow. OAuth2 is powerful, but it is also intricate. Every grant type exists for a purpose, and blurring those boundaries invites risk.
The vulnerability was resolved quickly and responsibly. But the lesson remains valuable for every engineering team:
Never trust a token that represents no user.
Never allow machine identities to access human data.
And always question implicit trust in authentication flows.
References
- OAuth 2.0 RFC 6749
- OWASP API Security Top 10
- Bug bounty methodology guides
- Public research on OAuth misconfigurations
- Developer documentation for machine-to-machine flows