File Inclusion Vulnerabilities for Bug Bounty: From Basics to Real-World Exploitation
A complete beginner-to-advanced guide on Local File Inclusion (LFI) and Remote File Inclusion (RFI), covering how they work, real-world exploitation techniques, and how developers should properly mitigate them.
Disclaimer
This article is written strictly for educational and defensive security purposes.
All techniques discussed must only be tested on applications you own or where you have explicit permission (such as authorized bug bounty programs).Do not test these techniques on random websites. Unauthorized testing is illegal.
Introduction
File Inclusion vulnerabilities are among the oldest yet still relevant classes of web application flaws. Despite being well-documented for decades, they continue to appear in modern applications-especially in legacy code, custom frameworks, and poorly reviewed features.
For bug bounty hunters, LFI and RFI are high-signal vulnerabilities:
- They often lead to sensitive data exposure
- They can escalate into Remote Code Execution (RCE)
- They are frequently underestimated or overlooked
This blog walks through file inclusion vulnerabilities from absolute basics to practical exploitation, with a clear bug bounty mindset.
What Are File Inclusion Vulnerabilities?
File Inclusion vulnerabilities occur when a web application dynamically loads files based on user-controlled input, without sufficient validation.
Internally, the application may use functions such as:
include()require()include_once()require_once()
When user input is passed directly into these functions, attackers can manipulate file paths to include unintended files.
There are two major categories:
- Local File Inclusion (LFI) - including files already present on the server
- Remote File Inclusion (RFI) - including files hosted on an external server
Local File Inclusion (LFI)
What Is LFI?
Local File Inclusion allows an attacker to read files that exist on the same server as the web application.
While LFI often starts as a read-only vulnerability, it can escalate into:
- Credential disclosure
- Source code leakage
- Log poisoning → RCE
- Session hijacking
How LFI Works (Simple Example)
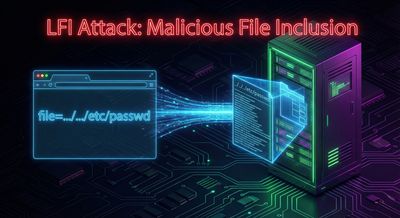
Consider this URL:
Internally, the application may be doing something like:
If the input is not sanitized, an attacker can manipulate the path:
If successful, the server responds with the contents of /etc/passwd.
Why /etc/passwd Is Used
- It exists on almost all Linux systems
- It is world-readable
- It confirms file read capability without breaking the app
This makes it a safe proof-of-concept for reporting.
Common LFI Exploitation Techniques
1. Path Traversal

Attackers traverse directories using ../:
Applications sometimes block simple traversal, so attackers try variations:
2. LFI via PHP Wrappers
PHP provides stream wrappers that are frequently abused.
Example:
This allows attackers to:
- Read PHP source code
- Bypass output restrictions
- Avoid code execution
3. LFI with Log Poisoning

This is where LFI becomes dangerous.
Step 1: Inject PHP into logs
Send a request with a malicious User-Agent:
Web servers log this value.
Step 2: Include the log file
If successful, the injected PHP executes.
Remote File Inclusion (RFI)
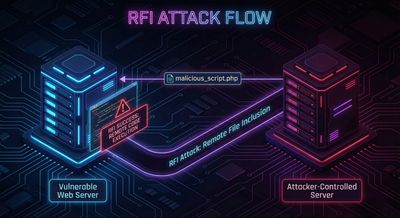
What Is RFI?
Remote File Inclusion allows attackers to include and execute files hosted on external servers.
RFI is generally more severe than LFI because it often leads directly to Remote Code Execution.
How RFI Works
Example vulnerable code:
Attacker payload:
If allow_url_include is enabled, the server fetches and executes the remote file.
Typical RFI Payload
Remote file (evil.php):
Execution:
How to Identify File Inclusion Vulnerabilities (Bug Bounty Methodology)
1. Parameter Discovery
Look for parameters like:
pagefileincludetemplatepathlangview
These are high-risk indicators.
2. Black-Box Testing
Without source code:
- Try
/etc/passwd - Try traversal sequences
- Observe error messages
- Watch for response length changes
3. Source Code Review (If Available)
Search for:
Check if allowlists or sanitization exist.
4. Controlled RFI Testing
Only in authorized environments:
- Use harmless payloads like
phpinfo() - Never deploy destructive shells
Real-World Bug Bounty Impact
File inclusion bugs often lead to:
- Database credential leaks
- Environment variable exposure
- Full server compromise
- Pivoting to internal services
Many high-severity bounties start as a “simple LFI”.
Mitigation Strategies (For Developers)

1. Never Trust User Input
Do not pass user input directly into file system functions.
2. Use Allow-Lists
Instead of:
Use:
3. Disable Dangerous PHP Settings
allow_url_include = Offallow_url_fopen = Off(when possible)
4. Proper File Permissions
- Logs should not be executable
- Sensitive files should not be web-accessible
5. Centralized Input Validation
Normalize paths and reject traversal patterns before processing.
Key Takeaways for Bug Hunters
- LFI is often underestimated but highly impactful
- Start with read-only proofs, then think about escalation
- Logs, backups, and config files are goldmines
- Old vulnerabilities still pay well when found responsibly
Conclusion
File Inclusion vulnerabilities are a perfect example of “simple input, catastrophic impact.”
They reward:
- Careful observation
- Patience
- Understanding of backend behavior
Whether you are a beginner bug hunter or an experienced researcher, mastering LFI and RFI is a must-have skill.
References
- OWASP File Inclusion Cheat Sheet
- CWE-98: Improper Control of Filename for Include/Require
- PortSwigger Web Security Academy - File Path Traversal
- PHP Manual - include() and require()